Overview: Stream Ciphers vs. Block Ciphers
Secure file transfer protocols like SFTP, FTPS, HTTPS, and WebDAVS encrypt data through symmetric key ciphers. These ciphers can be classified into two groups: stream ciphers and block ciphers. Today, we’ll discuss what a stream cipher is and what a block cipher is. We’ll also talk about the popular encryption algorithms that fall under each group.
If you don’t know what a cipher is, click that link to read a nice introduction. You might also want to learn more about symmetric and asymmetric encryption. Already familiar with them? Read on then.
What is a block cipher?
A block cipher is an encryption algorithm that encrypts a fixed size of n-bits of data – known as a block – at one time. The usual sizes of each block are 64 bits, 128 bits, and 256 bits. So for example, a 64-bit block cipher will take in 64 bits of plaintext and encrypt it into 64 bits of ciphertext. In cases where bits of plaintext is shorter than the block size, padding schemes are called into play. Majority of the symmetric ciphers used today are actually block ciphers. DES, Triple DES, AES, IDEA, and Blowfish are some of the commonly used encryption algorithms that fall under this group.
Popular block ciphers
DES – DES, which stands for Data Encryption Standard, used to be the most popular block cipher in the world and was used in several industries. It’s still popular today, but only because it’s usually included in historical discussions of encryption algorithms. The DES algorithm became a standard in the US in 1977. However, it’s already been proven to be vulnerable to brute force attacks and other cryptanalytic methods. DES is a 64-bit cipher that works with a 64-bit key. Actually, 8 of the 64 bits in the key are parity bits, so the key size is technically 56 bits long.
3DES – As its name implies, 3DES is a cipher based on DES. It’s practically DES that’s run three times. Each DES operation can use a different key, with each key being 56 bits long. Like DES, 3DES has a block size of 64 bits. Although 3DES is many times stronger than DES, it is also much slower (about 3x slower). Because many organizations found 3DES to be too slow for many applications, it never became the ultimate successor of DES. That distinction is reserved for the next cipher in our list – AES.
AES – A US Federal Government standard since 2002, AES or Advanced Encryption Standard is arguably the most widely used block cipher in the world. It has a block size of 128 bits and supports three possible key sizes – 128, 192, and 256 bits. The longer the key size, the stronger the encryption. However, longer keys also result in longer processes of encryption. For a discussion on encryption key lengths, read Choosing Key Lengths for Encrypted File Transfers.
Blowfish – This is another popular block cipher (although not as widely used as AES). It has a block size of 64 bits and supports a variable-length key that can range from 32 to 448 bits. One thing that makes blowfish so appealing is that Blowfish is unpatented and royalty-free.
Twofish – Yes, this cipher is related to Blowfish but it’s not as popular (yet). It’s a 128-bit block cipher that supports key sizes up to 256 bits long.
What is a stream cipher?
A stream cipher is an encryption algorithm that encrypts 1 bit or byte of plaintext at a time. It uses an infinite stream of pseudorandom bits as the key. For a stream cipher implementation to remain secure, its pseudorandom generator should be unpredictable and the key should never be reused. Stream ciphers are designed to approximate an idealized cipher, known as the One-Time Pad.
The One-Time Pad, which is supposed to employ a purely random key, can potentially achieve “perfect secrecy”. That is, it’s supposed to be fully immune to brute force attacks. The problem with the one-time pad is that, in order to create such a cipher, its key should be as long or even longer than the plaintext. In other words, if you have 500 MegaByte video file that you would like to encrypt, you would need a key that’s at least 4 Gigabits long.
Clearly, while Top Secret information or matters of national security may warrant the use of a one-time pad, such a cipher would just be too impractical for day-to-day public use. The key of a stream cipher is no longer as long as the original message. Hence, it can no longer guarantee “perfect secrecy”. However, it can still achieve a strong level of security.
Popular stream ciphers
RC4 – RC4, which stands for Rivest Cipher 4, is the most widely used of all stream ciphers, particularly in software. It’s also known as ARCFOUR or ARC4. RC4 steam chiphers have been used in various protocols like WEP and WPA (both security protocols for wireless networks) as well as in TLS. Unfortunately, recent studies have revealed vulnerabilities in RC4, prompting Mozilla and Microsoft to recommend that it be disabled where possible. In fact, RFC 7465 prohibits the use of RC4 in all versions of TLS.
These recent findings will surely allow other stream ciphers (e.g. SALSA, SOSEMANUK, PANAMA, and many others, which already exist but never gained the same popularity as RC4) to emerge and possibly take its place.
Disabling weak ciphers
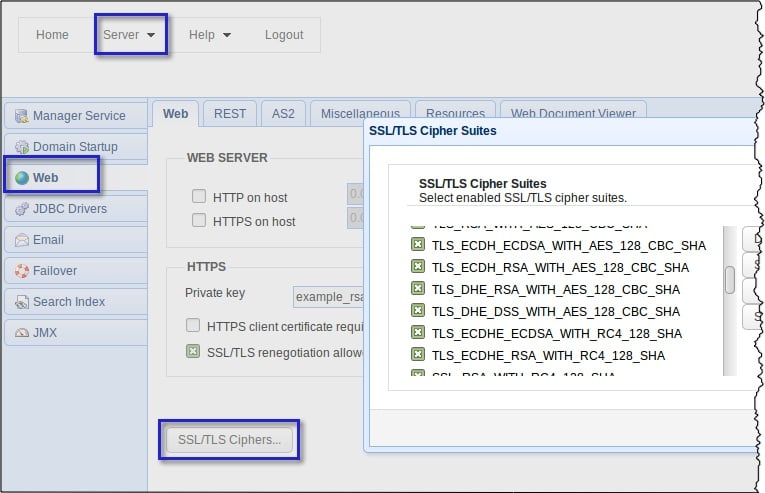
On JSCAPE MFT Server, you may disable cipher suites using RC4 (or any encryption algorithm you deem too weak, for that matter) …
From HTTPS:
Navigate into Server > Settings > Web > SSL /TLS Ciphers.
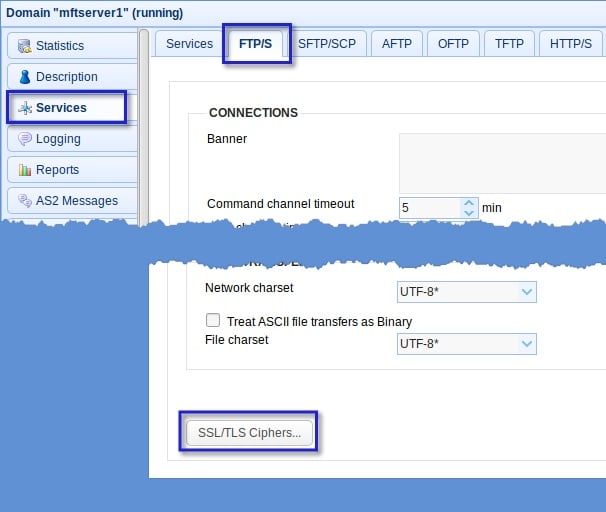
From FTPS:
Go to Services > FTP/S > SSL/TLS Ciphers
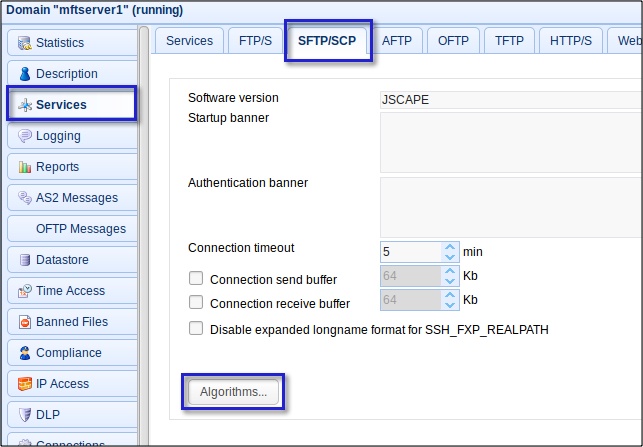
From SFTP/SCP
Go to Services > SFTP/SCP > Algorithms
There are a couple of things you need to consider when disabling ciphers and other algorithms on your MFT server. I suggest you read the article Setting SFTP Algorithms On Your SFTP Server to be enlightened on the matter.
That’s it for this topic. You might also want to read the following articles:
What Is A Digital Certificate?
How To Get Your MFT Server To Email You About Last Night’s Download
How To Send Large Files Through Email
Get Started
Download a free, fully functional evaluation edition.
- Request a free trial
- Connect with a JSCAPE product expert
- Experience the power of JSCAPE MFT Server, a multi-protocol, platform-independent managed file transfer solution users are most likely to recommend, according to G2.
Frequently Asked Questions
What is a block cipher?
A block cipher is an encryption algorithm that encrypts bits of data (known as a block) at one time. The usual sizes of each block are 64 bits, 128 bits or 256 bits. So, for example, a 64-bit block cipher will take in 64 bits of plaintext and encrypt it into 64 bits of ciphertext. The majority of the symmetric ciphers used today are block ciphers, including DES, Triple DES, AES, IDEA and Blowfish.
What is a stream cipher?
A stream cipher is an encryption algorithm that encrypts one bit or byte of plaintext at a time. It uses an infinite stream of pseudorandom bits as the key. For a stream cipher implementation to remain secure, its pseudorandom generator should be unpredictable, and the key should never be reused.
What is the difference between block cipher and stream ciphers?
Secure file transfer protocols like SFTP, FTPS, HTTPS and WebDAVS encrypt data through symmetric key ciphers. These ciphers can be classified into two groups: stream ciphers and block ciphers. A block cipher encrypts in blocks of 64 bits, 128 bits or 256 bits, whereas a stream cipher encrypts one bit or byte of plaintext at a time.