Category: JSCAPE MFT
-

The IT/OT divide: Is your enterprise blind to a critical threat?
Your enterprise security strategy may be incomplete.
Learn More
-

From unplanned downtime to unmatched competitiveness
Why AI is making OT/IT convergence a C-Suite imperative.
Learn More
-

NERC-CIP: From regulatory burden to business catalyst
Go beyond compliance and uncover transformational data with JSCAPE by Redwood.
Learn More
-

JSCAPE by Redwood, version 2025.3: New UI continues to make a splash
Dive back into JSCAPE by Redwood with version 2025.3, bringing more modern UI updates to make using and navigating JSCAPE more intuitive.
Learn More
-

Weathering the economic storm: Expert support is your enterprise file transfer system’s lifeline
The global economic landscape can be described by one word: “uncertain”. Lingering effects from the 2020 pandemic, combined with new waves of…
Learn More
-

Escape the grip: Why flexible MFT is key to enterprise agility
Break free from costly vendor lock-in Let’s be blunt: some MFT vendors have built product suites that are less about true partnership…
Learn More
-

Avoid downtime and threat actors: Getting the best of both worlds in MFT
For enterprise organizations relying on managed file transfer (MFT) solutions, cybersecurity often feels like an arms race. The need to patch MFT…
Learn More
-

Consolidate, deploy and thrive: JSCAPE’s formula for MFT success in uncertain times
Global enterprises today are navigating a landscape marked by significant economic volatility. Fluctuating markets, shifting trade policies and persistent economic uncertainty are…
Learn More
-

5 signs your MFT vendor is capable of mitigating zero-day data breaches
Zero-day exploits are currently one of the most prevalent cyber attacks impacting file transfer solutions. We won’t go into specifics, but a…
Learn More
-

5 ways JSCAPE ensures 24/7/365 security and compliance for banking file transfers
Banking institutions, including commercial, retail and investment banks, frequently exchange files with various trading partners, which typically include customers, clearinghouses, corporate clients,…
Learn More
-

How to protect consumer data and ensure data security for banks with JSCAPE
Banks store, process and transfer vast amounts of sensitive consumer data. This may include financial information, credit card data, personally identifiable information…
Learn More
-

The compliance imperative: why secure file transfers are non-negotiable in 2025
This year, the stakes for regulatory compliance are higher than ever. Organizations face an increasingly complex landscape of data protection and privacy…
Learn More
-
Replace root path of the users using ReplaceUsersPath action
This custom trigger action is used to replace the users default root path.
Learn More
-
Replace path of all users using ReplaceUsersPath action
This custom trigger action is used to replace all users path.
Learn More
-

MFT servers explained: why your business needs one now
Increased IT complexity, regulatory compliance obligations and senior management demands for greater efficiency are rapidly rendering general-purpose file transfer solutions incapable of…
Learn More
-
How to set up a HTTPS file transfer
HTTPS file transfers combine user-friendly file management with enterprise-level security. Supported by SSL/TLS encryption, they ensure data confidentiality, authentication, and integrity. No…
Learn More
-

Using SFTP with the Cloud
For several decades, SFTP, which stands for Secure File Transfer Protocol or SSH File Transfer Protocol, has been arguably the most widely…
Learn More
-

What is managed file transfer (MFT)?
Managed file transfer is a category of solutions that enable secure, centrally managed, regulatory-compliant, automated, reliable and efficient data movement. An MFT…
Learn More
-
What is the fastest way to transfer large files over the internet?
When your business processes involve large files that need to cross the internet in the fastest way possible, look beyond traditional methods…
Learn More
-
What is MFTaaS? an introduction to managed file transfer SaaS
Managed file transfer as a service (MFTaaS) is revolutionizing file transfer workflows by improving efficiency and security while reducing cost and maintenance.…
Learn More
-

Unlock your potential: JSCAPE courses now available in redwood university!
Have you heard the exciting news!? Redwood University recently expanded its training resources for JSCAPE by Redwood customers. Whether you’re a seasoned…
Learn More
-
JSCAPE 2024.2: more enhancements, big impact
JSCAPE 2024.2 is here, with numerous feature enhancements making a big impact. The newest features are designed to make using JSCAPE by…
Learn More
-

How to use microsoft integrations with JSCAPE managed file transfer
Flexibility isn’t limited to gymnasts. While JSCAPE might not be doing the splits, it stays flexible with built-in integrations to solutions you…
Learn More
-

When SFTP isn’t enough — signs you need an MFT solution
If SFTP is limiting your operations, consider an MFT solution for automation, protocol versatility, and advanced security. Explore our detailed blog post…
Learn More
-
SFTP vs. MFT: Benefits of an MFT solution
When you first start identifying the right file transfer solution for your organization, you’ll encounter these two acronyms: MFT and SFTP. SFTP…
Learn More
-

MFT gateway vs. SFTP server: key features and differences
Some people are unsure of the difference between MFT Gateway and SFTP server. These are two distinct applications with different core functionalities.…
Learn More
-

Dedicated to the integrated: new release for JSCAPE MFT server 2023.3 and MFTaaS 2023.2
As 2023 comes to a close, JSCAPE is excited to announce more integrations for MFT Server and MFTaaS, as well as a…
Learn More
-

JSCAPE version 2023.1 and 2023.2 now available
JSCAPE 2023.1 | Managed File Transfer as a Service (MFTaaS) JSCAPE is now available in SaaS, expanding the choices of environments in…
Learn More
-

Is JSCAPE MFT server multilingual?
As one of the easiest-to-use managed file transfer solutions available, JSCAPE MFT is able to support a variety of users, including those…
Learn More
-

Finding secure MFT: Considerations for enterprise buyers
Managed file transfer (MFT) is an essential component of secure data exchange for businesses and enterprise organizations. Whether you are transferring sensitive…
Learn More
-
Forward proxy vs. reverse proxy servers
Forward proxies and reverse proxies intermediate between clients and servers to improve security, control, policy enforcement and network performance. Forward proxies act…
Learn More
-

How To Automate An SFTP File Transfer
Automated secure file transfer protocol (SFTP) file transfers are traditionally done through scripts, but there’s a much easier way. In this tutorial,…
Learn More
-

How to set up automated AS2 file transfers
Overview In an earlier quickstart guide to setting up an AS2 server, we featured a manual method for sending EDI messages. Because…
Learn More
-
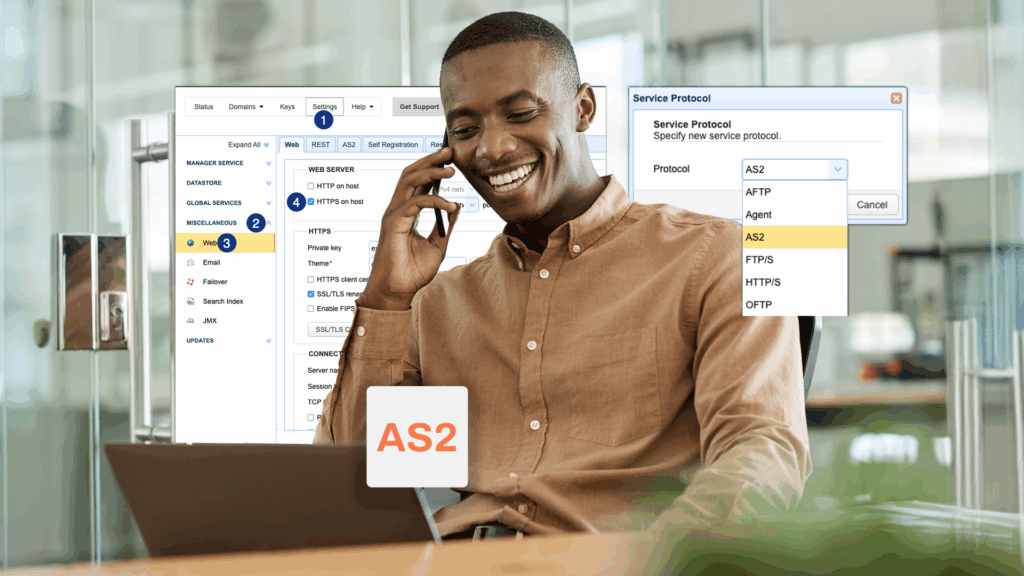
How to setup an AS2 server with JSCAPE: a QuickStart guide
In this tutorial, you’ll learn the basic steps for setting up an Applicability Statement 2 (AS2) server. While the final outcome will…
Learn More
-

Downloading files periodically from a trading partner
Overview In this post we’re going to show you how to download files periodically from a trading partner. For this particular example,…
Learn More
-
Monitoring a remote SFTP server for newly added files
Most users of JSCAPE MFT Server are already familiar with directory monitors. You often use it to monitor a directory for newly…
Learn More
-
How to copy multiple files from s3 to azure data lake storage
In this tutorial, I’m going to show you how to copy multiple files automatically from AWS S3 to Azure Data Lake Storage…
Learn More
-

How to push files from local to azure data lake based on an event
Azure Data Lake is an excellent option for storing massive amounts of unstructured, semi-structured, and structured data in the cloud. One of…
Learn More
-

How to automatically transfer files from SFTP to azure blob storage via trading partner
In a previous post, we taught you how to automatically transfer files from SFTP to Azure Blob Storage using a JSCAPE MFT…
Learn More
-

How to automatically transfer files from SFTP to azure blob storage via network storage
Let’s say you have trading partners who can only transfer files to you via SFTP. Incidentally, you also happen to have an…
Learn More
-

Three ways to generate OpenPGP keys
JSCAPE MFT Server makes it easy to strengthen secure file transfers with OpenPGP encryption and decryption. But before you can protect your…
Learn More
-
JSCAPE MFT server 12.1.11 (Patch)
JSCAPE MFT Server Patch 12.1.11 was released to address the following issue:
Learn More
-

How to use amazon s3 as storage for your MFT server
Overview A couple of weeks ago, we compared the advantages and disadvantages of using Amazon S3 and local storage as file storage…
Learn More
-

Customising the web user interface of your HTTP/S file transfer service
When you first launch your web file transfer service on JSCAPE MFT Server, you’ll notice that the web user interface has the…
Learn More
-
What is HTTP strict transport security (HSTS)?
When I first read about HSTS, my first reaction was, “What’s this? A replacement for HTTPS? Considering the ubiquity of HTTPS, shouldn’t…
Learn More
-
How to set up an HTTP file transfer
A hypertext transfer protocol (HTTP) file transfer, which is also known as a web file transfer, is one of the most user-friendly…
Learn More
-
JSCAPE MFT server 12.1.10.392 (Patch)
JSCAPE MFT Server Patch 12.1.10.392 was released to address the following issues:
Learn More
-

That free FTP server might cost more than you think
As you scout for the most cost-effective way of transmitting files with your business units and trading partners, among the many file…
Learn More
-
JSCAPE MFT server 12.1.10.391 (Patch)
JSCAPE MFT Server Patch 12.1.10.391 was released to address this issue:
Learn More
Browse by category
-
(23)
-
(43)
-
(7)
-
(39)
-
(57)
-
(40)
-
(19)
-
(622)
-
(3)
-
(390)
-
(106)
-
(5)
-
(19)
-
(199)
-
(22)
-
(86)