A forward proxy regulates client access to the internet, enhancing security and policy enforcement within an internal network. A reverse proxy, manages external requests to servers, offering load balancing and concealing server identities for added security. While forward proxies protect internal clients, reverse proxies safeguard servers from external access and threats.
Forward proxies and reverse proxies intermediate between clients and servers to improve security, control, policy enforcement and network performance. Forward proxies act on behalf of clients, whereas reverse proxies act on behalf of servers. In this post, we’ll take a closer look at the similarities and differences between these two important network security solutions. The information you’ll gain from this post can help you streamline your network-dependent business processes and improve your organization’s security posture.
Of the two types of proxy servers, the forward proxy server or forward proxy is more popular among end users, especially those who grew up in the dial-up internet era. During that period, many users had to tinker with their proxy settings to get a good internet connection. When people used the term “proxy” back then, they normally meant a forward proxy.
With that in mind, let’s start our discussion with the forward proxy.
The forward proxy server
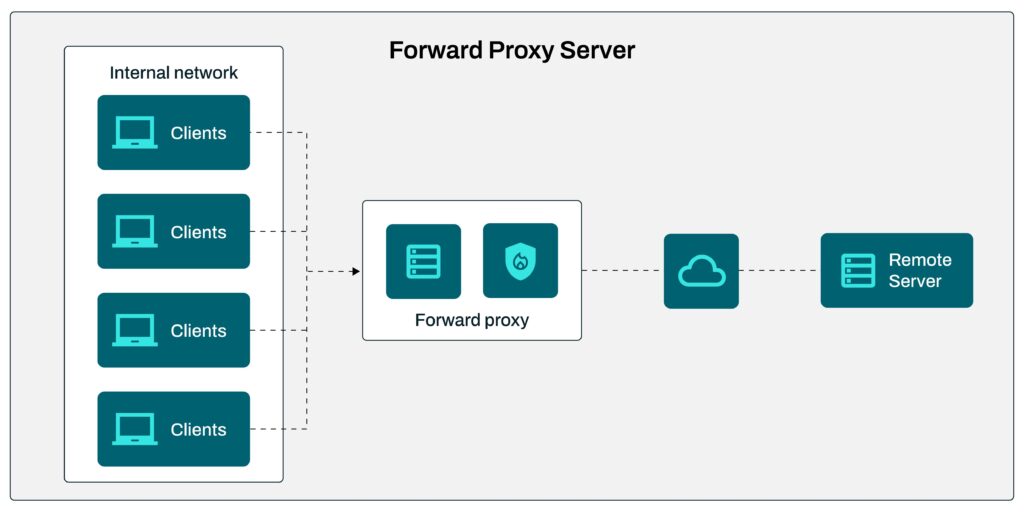
A forward proxy acts as a middleman between clients in an internal network and different servers on the internet. It intercepts outbound client requests to a remote server and then, depending on how the proxy settings are configured, allows or denies that request.
If a request is allowed, it’s forwarded to the remote server. From the server’s point of view, the request originates from the proxy. As a result, it sends its reply to the proxy’s IP address. Since a forward proxy sends requests on behalf of clients, it essentially hides those clients’ IP addresses. Once the server sends back a response, the proxy recognizes that response and then sends back that response to the client that issued the request.
Because a forward proxy hides client IP addresses, you might be thinking it’s similar to a virtual private network (VPN). However, that’s actually the only similarity between these two network solutions.
Want a closer look? Get access to JSCAPE when you request a trial.
While a VPN encrypts data, a forward proxy does not. Also, a VPN usually operates at the network layer of the Open Systems Interconnection (OSI) model, whereas a forward proxy typically operates at the application layer. We’re sometimes asked whether proxies and VPNs are the same, so we thought it would be good to put that question out of the way first.
Normally, a forward proxy works in conjunction with a firewall to enforce security policies such as content filtering, URL filtering and user access to remote sites. Some proxies are also equipped with caching functionality, which speeds up requests by storing frequently accessed content locally on the proxy server.
How forward proxy works: Use case
As the head of IT for a large company, you’ve been tasked to implement content filtering for users who access the web. You decide to use a forward proxy for this purpose. When a forward proxy is used to access web servers on behalf of clients, it’s known as a web proxy.
You deploy your forward proxy along with a firewall at your network perimeter. When users attempt to access external websites, their requests pass through that proxy. The forward proxy inspects the requests and determines whether to allow or deny access based on your content filtering rules. Your filtering rules may, for instance, block access to social media, gaming, gambling and pornographic websites.
If the URL, IP address or hostname of the destination web server doesn’t fall under any of those categories, the request is allowed to pass through. On the other hand, if it does, the request is blocked. In the context of forward proxies, the web server in question is also known as an origin server since it hosts the original versions of the resources being accessed.
Upon receiving the request, the origin server retrieves the requested resources and sends them back to your web proxy. Your proxy then forwards the content back to the requesting client, thereby allowing users to access web resources in a safe and secure manner.
How reverse proxy server works
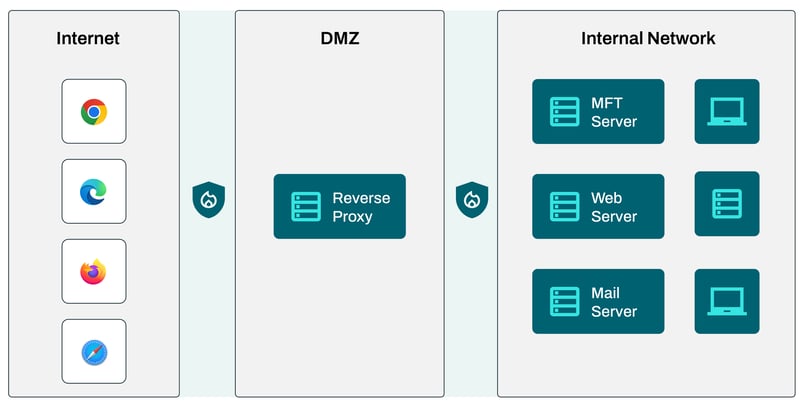
Like a forward proxy, a reverse proxy also intermediates between clients and servers and sits at the network perimeter. However, unlike in the previous scenario, it’s the servers that are located in the internal network.
The reverse proxy intercepts incoming requests from the internet, presumably from clients outside the internal network. If the requests meet the reverse proxy’s access control policies, they are forwarded to the destination backend servers running in the internal network.
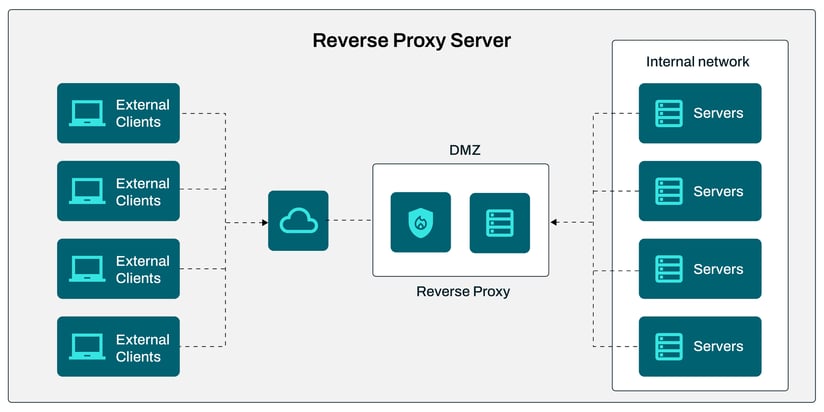
When a backend server responds to a request, the response is first sent to the reverse proxy, which then forwards the response to the requesting client. Again, since external clients only interact with the reverse proxy, the IP addresses of the backend servers are unknown to outsiders. This level of obscurity makes it difficult for external threats to devise attacks against those servers.
Although external clients that pass through a reverse proxy mostly interact with the proxy, authentication takes place at the backend servers. This means login credentials are not stored at a proxy. This is also good from a cybersecurity standpoint because, as stated earlier, reverse proxies are deployed at your network perimeter, usually in your demilitarized zone (DMZ). So, even if external threats can reach your reverse proxy, those threats won’t be able to find any login credentials to your internal servers there.
Reverse proxies and load balancing
In addition to their proxying capabilities, modern reverse proxies like JSCAPE MFT Gateway by Redwood have built-in load balancing functionality. These reverse proxies employ load balancing algorithms to distribute incoming traffic across a cluster of redundant backend servers in an internal network. Since incoming traffic is shared among multiple redundant servers, the risk of a single server getting overloaded is substantially reduced.
For this reason, load balancing-capable reverse proxies can be used to deliver high availability (HA) services. For instance, you can employ this type of reverse proxy to deliver a high availability Secure File Transfer Protocol (SFTP) service. High availability clusters like the one described above are scalable.
Experience automated load balancing for enhanced performance and active-active availability that scales as your demands increases. [ Request a Trial ]
Scalability capabilities enable a cluster to readily accept additional servers, a.k.a. “nodes,” to increase the cluster’s capacity. The more nodes you add to a cluster, the more resilient the cluster will be.
This will make the cluster more capable of supporting seasonal high traffic volume or even withstanding a Distributed Denial-of-Service attack or DDoS attack.
Sample reverse proxy use case
As part of your company’s Payment Card Industry Data Security Standard (PCI DSS) regulatory compliance initiatives, you’ve been tasked to ensure that no credit card data is stored in your DMZ. Unfortunately, in your current setup, you have public-facing servers in your DMZ that serve external clients. Some of those public-facing servers do store credit card data.
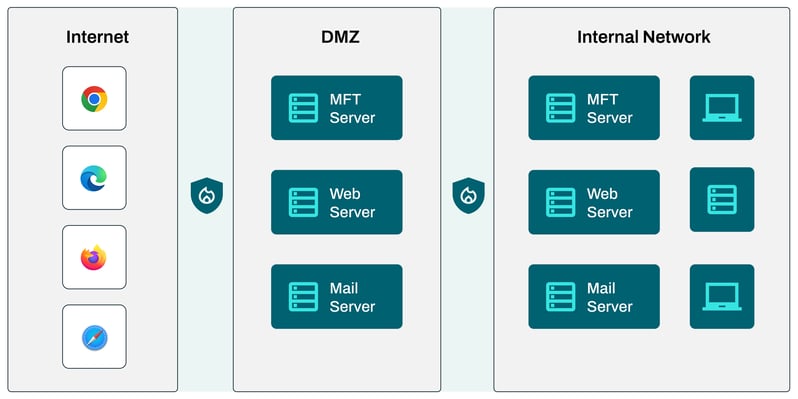
To address the issue, you decide to use a reverse proxy.
By deploying a reverse proxy at your DMZ, you’re able to:
- Move all previously public-facing servers into your internal network,
- Close all inbound ports on your internal firewall (the one on the right in the diagram below) and
- Limit access to your internal servers to the reverse proxy.
JSCAPE MFT Gateway – a reverse proxy and load balancer built for file transfer workflows
JSCAPE MFT Gateway is a reverse proxy and load balancer that readily integrates with JSCAPE MFT by Redwood. Combined, they enable you to achieve secure, highly-performant, highly available, automated and compliant file transfer workflows and business processes.
JSCAPE MFT Gateway runs on all major operating systems, including Microsoft Windows, Linux, UNIX and macOS. It comes with a centralized graphical administrative user interface and a REST API that allows you to manage JSCAPE MFT Gateway programmatically.
Get a free trial of JSCAPE MFT Server.
Frequently Asked Questions
How does a forward proxy work?
A proxy service’s purpose is to act on behalf of another machine, such as a client, web server, or other backend server. A forward proxy provides these proxy services to one or more clients. Whenever a request comes into a server from a client, it has to pass through a forward proxy. The forward proxy usually has a set of configurations that provide rules on whether or not the request will be allowed through.
What is a reverse proxy?
A reverse proxy is the opposite of a forward proxy. A forward proxy intermediates on behalf of a client/requesting host. A reverse proxy provides proxy services on behalf of servers. It accepts requests from external clients, often acting as a load balancer. Reverse proxies provide a single point of access and control, and are normally configured alongside firewalls to control traffic and requests directed to a group of internal servers.
What is PCI-DSS?
PCI DSS is short for “payment card industry data security standard.” It is a set of standard global security regulations created to prevent credit card fraud. The goal of PCI DSS is to protect cardholder data with standard rules for payment processing. PCI DSS regulations make sure that anyone who processes, stores, accepts, or transmits credit card data does so in a secure way.