Category: Security
-

Easy Sarbanes-Oxley Act (SOX) compliance through secure protocols
Learn more from the experts at JSCAPE by Redwood
Learn More
-

Protect cardholder data: PCI DSS compliance guide
Learn more from the experts at JSCAPE by Redwood
Learn More
-

How to generate client certificates for SSL/TLS authentication
Learn more from the experts at JSCAPE by Redwood
Learn More
-

9 best practices for secure document transfers in business operations
Learn more from the experts at JSCAPE by Redwood
Learn More
-

What is MFA authentication and why it’s crucial for file transfer security
Learn more from the experts at JSCAPE by Redwood
Learn More
-

What is SSO and how does it work? a guide for file transfer professionals
What is Single Sign-On (SSO)?
Learn More
-
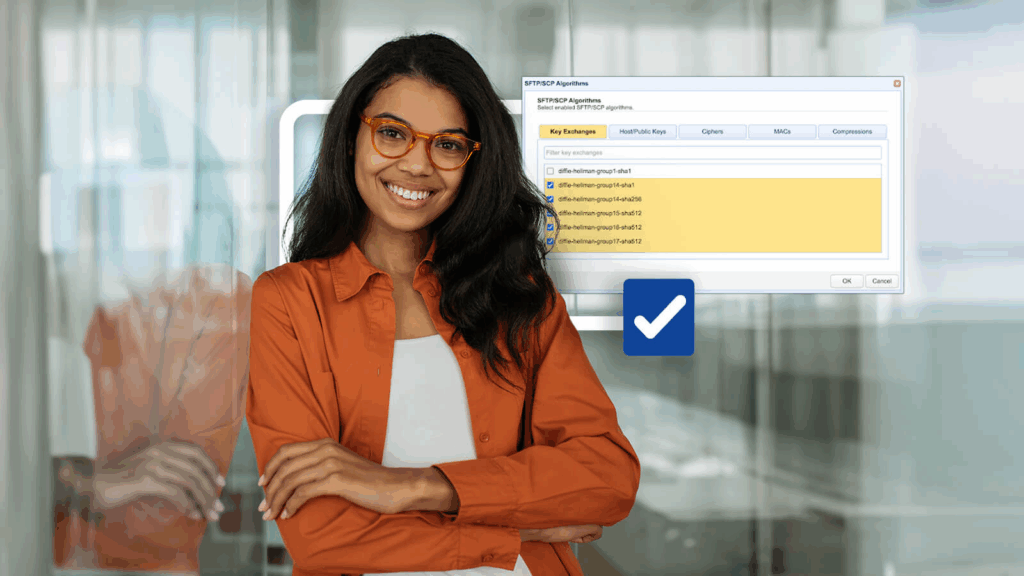
Fixing SSH/SFTP client connection issues involving Diffie-Hellman-Group1-SHA1
When you’re troubleshooting connectivity issues between Secure Shell (SSH)/Secure File Transfer Protocol (SFTP) clients and servers, it pays to inspect the error…
Learn More
-

13 data security solutions: how data security can be implemented when transferring files
Why do some organizations excel in protecting their sensitive data during file transfers while others fall prey to cyber threats? What constitutes…
Learn More
-

PGP vs GPG: the key differences explained
Pretty Good Privacy (PGP) and GNU Privacy Guard (GPG) are two cryptographic software tools that enable data encryption, authentication, and integrity. These…
Learn More
-

What is client certificate authentication?
Overview How do you strengthen a server’s user authentication system? Well, one solution would be to add another authentication method. Most servers…
Learn More
-
Perform directory virus scan using avast
This custom trigger action performs a virus scan against a directory using Avastanti-virus software. Downloads Source code and build instructions
Learn More
-
Perform directory virus scan using kaspersky
This custom trigger action performs a virus scan against a directory using Kaspersky anti-virus software. Downloads Source code and build instructions
Learn More
-
Update virus database definitions using kaspersky
This custom trigger action updates the virus database definitions using Kaspersky anti-virus software. Downloads Source code and build instructions
Learn More
-
How to perform an antivirus scan with kaspersky
This custom trigger action performs a virus scan against a file using Kaspersky anti-virus software. Downloads Source code and build instructions
Learn More
-
How to scan a file with avast antivirus
This custom trigger action performs a virus scan against a file using Avast anti-virus software. Downloads Source code and build instructions
Learn More
-
Should we start using 4096 bit RSA keys?
Theoretically, RSA keys that are 2048 bits long should be good until 2030. If so, isn’t it a bit early to start…
Learn More
-

The SSH/SFTP key fingerprint and its role in server authentication
When users attempt to connect to your Secure File Transfer Protocol (SFTP) server for the first time, they’ll see an alert indicating…
Learn More
-

Demystifying SMTP ports: when to use port 25, 587, 465 or 2525
When you’re tasked with configuring Simple Mail Transfer Protocol (SMTP) settings to connect to an email server, you need to get two…
Learn More
-

How to import a client certificate to firefox
Overview Client certificate authentication is very suitable for highly secure HTTPS connections. But for this type of authentication to work, the server…
Learn More
-

How do digital certificates work – an overview
In our previous post, we discussed what a digital certificate is. But how do digital certificates work? Today, we will give you…
Learn More
-

DSA vs. RSA encryption – which works best for file transfers?
Overview: DSA vs. RSA During the process of generating server keys, client keys, or PGP keys in the JSCAPE MFT Server Manager,…
Learn More
-

How to prevent sniffer attacks with encrypted FTP
Overview A lot of people who often send files love FTP. The File Transfer Protocol allows users to transmit volumes of files…
Learn More
Browse by category
-
(23)
-
(43)
-
(7)
-
(44)
-
(57)
-
(40)
-
(19)
-
(623)
-
(3)
-
(390)
-
(106)
-
(6)
-
(19)
-
(199)
-
(22)
-
(86)
