JSCAPE MFT Server encrypted file transfer protocols like SFTP and those secured through TLS (e.g. HTTPS, FTPS, AS2, OFTP, and WebDAVS) can be configured for FIPS compliance. Since this is a function that isn’t switched on by default, you might wonder if it’s necessary to enable it at all.
What is FIPS compliance?
FIPS compliance means adherence to standards specified by the Federal Information Processing Standards (FIPS) Publication. In the context of file transfers, it typically means compliance with FIPS 140-2, entitled ‘Security Requirements for Cryptographic Modules’. Basically, FIPS 140-2 defines what cryptographic algorithms and strengths are acceptable for transmitting sensitive data.
These standards are important because secure file transfer solutions like JSCAPE MFT Server support a wide range of cryptographic algorithms and strengths but not all of them are suitable for the kind of data some organizations like the military and government agencies often transmit. Click here to request a free trial of JSCAPE.
What kinds of organizations need it?
FIPS 140-2 requirements mainly apply to:
1. The US military,
2. Government agencies, and
3. Vendors, contractors, suppliers and other organizations who exchange data with the US military or government agencies.
If your organization belongs to the list above, you can’t just transmit data using any file transfer protocol. In fact, it’s not enough to simply apply encryption or use encrypted protocols like SFTP. You need to make sure that the cryptographic algorithms (e.g. ciphers, hash functions) you use in securing your file transfers are actually FIPS 140-2-approved algorithms.
If we’re not a government agency, do we need to enable FIPS?
Organizations who don’t belong to the list above aren’t compelled to enable the FIPS compliance feature on their managed file transfer servers. However, if you want to enable it so you could take advantage of the security benefits of stronger cryptographic algorithms, then feel free to do so.
Just bear in mind though, because enabling FIPS compliance means restricting your supported cryptographic algorithms to a (considerably) narrower selection, you might encounter interoperability issues. If a business partner’s’ file transfer application only supports (relatively) weak ciphers or non-FIPS-compliant ciphers, that application won’t be able to exchange files with you.
But the bigger dilemma comes when you have to transact with BOTH government agencies and non-government agencies. That could mean you would have to enable strong encryption for the former and (relatively) weak encryption for the latter.
This can be addressed easily if you’re using JSCAPE MFT Server because FIPS compliance for most encrypted file transfer protocols (except HTTPS) can be enabled at the domain level. This means, you can enable FIPS compliance on domains you’ll be using to transact with government and military agencies and disable FIPS on domains you’ll be using for other organizations.
Enabling your managed file transfer server for FIPS compliance
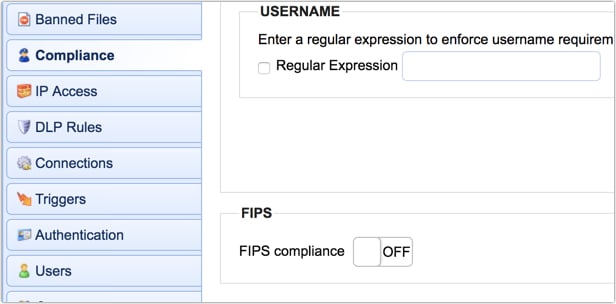
You can find instructions for enabling FIPS compliance in the domain level here. Again, that doesn’t include HTTPS file transfers. If you want to enable FIPS compliance for your HTTPS data transfers, you can do that in Settings > Web > Web > Enable FIPS compliance.
Related posts
Meeting AES 256 Encryption Requirements For Data In Transit
Choosing Key Lengths for Encrypted File Transfers
Guide to HIPAA Compliant File Transfers
Guide to PCI DSS Compliant File Transfers
Looking for a file transfer server that supports FIPS 140-2-approved algorithms? Request the free, fully-functional evaluation edition of JSCAPE Managed File Transfer Server now.


