When it comes to moving files across networks, not many protocols are as established as File Transfer Protocol (FTP), File Transfer Protocol Secure (FTPS) and Secure File Transfer Protocol (SFTP). Organizations rely on these protocols to move files internally — between branches or departments — or externally to suppliers, customers or trading partners.
While these acronyms and even their unabbreviated forms look strikingly similar, the protocols themselves have different characteristics under the hood. Understanding the main differences can help you make informed decisions when choosing the right protocol for your business or a specific use case.
Before we proceed, allow me to deviate a bit. Are you by any chance looking for a file transfer solution and are here to find out which protocol is best for the job? If so, you might want to check out JSCAPE by Redwood. JSCAPE is an advanced managed file transfer solution that supports all three protocols. You can request a free trial of JSCAPE and compare all three protocols live in your test environment. I apologize for the interruption. Let’s proceed with the article.
FTP is the oldest among the three, so let’s cover it first.
What is FTP?
FTP, which has been in existence since the early days of the internet, was built for a single purpose: to transfer files across a network. It runs on top of Transmission Control Protocol (TCP), which ensures that data is sent in a reliable manner. TCP does this by breaking down files into packets, retransmitting any packets that are lost, and reassembling packets in the correct order. FTPS and SFTP also use TCP for this same reliability functionality.
Data exchange
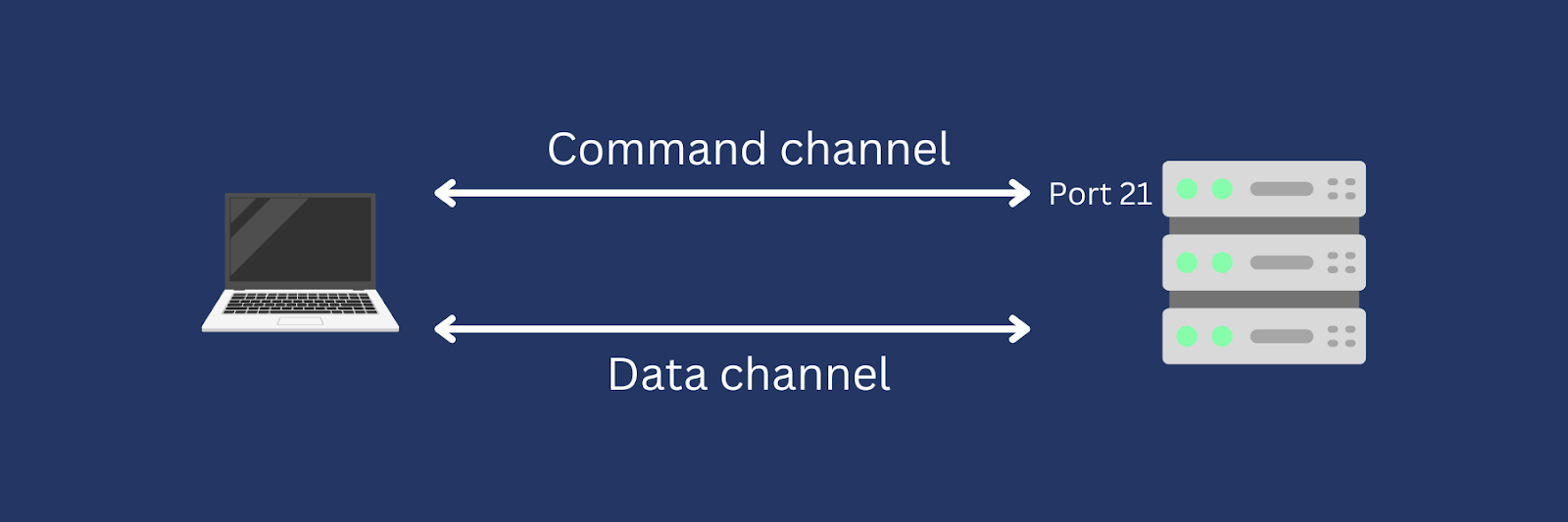
To transfer files using FTP, you’ll need an FTP client and an FTP server. You typically use an FTP client to connect to the server and initiate the file transfer session. In most cases, you would connect to the server at port 21. This is the port number a standard FTP service listens on for incoming connection requests.
Technically speaking, port 21 is actually the FTP service’s command channel (a.k.a. control channel). This is the channel where FTP command requests and responses are sent. FTP has a separate data channel for sending the actual data, i.e., your files. In other words, FTP uses two channels, one for commands and another for data.
Firewall considerations
Unless you deliberately opt for a non-standard port number, FTP’s control channel port number should be port 21. The data channel port number, however, can vary. It depends on the data connection mode used, which can be active mode or passive mode. A discussion on these FTP data connection modes is beyond the scope of this article. That being said, we’ve covered that discussion in detail in the blog post “Active vs. passive FTP simplified.”
Because of this added complexity involving FTP modes, you may encounter challenges when setting up firewall rules for your FTP connections. It’s not as simple as opening port 21. If you intend to use FTP or FTPS in your organization, I highly recommend you read the post on active and passive FTP modes I just shared above.
Security features
Although FTP can be quite challenging to configure on your firewall, that’s not enough reason to avoid it. The main reason to avoid FTP is its lack of security features. While FTP supports basic password-based authentication, which requires users to submit a user ID (a.k.a. username) and a password, these login credentials are sent in plain text.
That means a hacker eavesdropping on your network can capture those credentials with a packet sniffer and then use those credentials to gain unauthorized access to your FTP server. If you want to know how that type of cyber attack, also known as a man-in-the-middle attack, works and how to prevent it, read our blog post “How to prevent sniffer attacks with encrypted FTP.”
Earlier, when you read that FTP “was built for a single purpose: to transfer files across a network,” you might have wondered — aren’t FTPS and SFTP built for this purpose as well? Indeed, their main purpose is to transfer files across a network, but they’re also meant to do so in a secure manner.
The absence of this single attribute in FTP is one big reason why FTP implementations are now being replaced with secure FTP alternatives such as FTPS and SFTP.
What is FTPS?
FTPS is essentially a secure version of FTP. It has all the main properties of the FTP protocol, but reinforced with security features that provide data confidentiality, client and server authentication and data integrity. These features are necessary if a file transfer protocol is to be used in business processes or any transaction that involves sensitive data.
Data exchange
In terms of pure file transfer or data exchange operations, FTPS functions pretty much the same way as FTP. It uses port 21 as its standard command channel listening port. FTPS clients must establish connections with an FTPS server before transferring files. And then once a connection is established, the client and server communicate through two channels — a control channel for sending commands and a data channel for sending files.
Firewall considerations
Since FTPS is based on FTP, it inherits most of FTP’s properties. Unfortunately, that includes FTP’s dual channel and dual data connection mode properties, which make firewall configurations quite challenging. If you want to know how to tackle those challenges, again, review the blog post “Active vs. passive FTP simplified.”
Security features
As indicated earlier, the main difference between FTPS and FTP is the lack of security features in the latter. Unlike FTP, FTPS provides the following security capabilities:
- Data confidentiality: Achieved through data-in-transit encryption, which prevents man-in-the-middle attackers from obtaining useful information from intercepted FTPS connections.
- Client and server authentication: Achieved through client and server certificates. In FTP, only servers can authenticate clients, typically through password-based authentication. In FTPS, clients can also authenticate servers, allowing those clients to verify whether they’re connecting to the right server before uploading any files.
- Data integrity: Achieved through mechanisms like HMAC (Hash-based Message Authentication Code) that use hash algorithms to verify the integrity of transmitted data.
All FTPS security features are derived from Transport Layer Security (TLS), the same cryptographic protocol used by secure websites running Hypertext Transfer Protocol Secure (HTTPS). Before the emergence of TLS, FTPS implementations relied on TLS’s predecessor, Secure Sockets Layer (SSL), for those security capabilities. In fact, the abbreviation FTPS also used to mean FTP-SSL. Today, many TLS settings are still labeled as SSL/TLS, even if SSL is no longer used. What can we do? Old technologies simply die hard.
What is SFTP?
While FTP and FTPS are closely related, SFTP is an entirely different protocol with no association with FTP. Rather, it’s associated with Secure Shell (SSH), the network protocol many IT administrators use to remotely access UNIX and UNIX-based operating systems like Linux and macOS. In fact, SFTP derives its security functionality directly from SSH. Most SSH installations also include SFTP by default. For these reasons, SFTP is often referred to as SSH File Transfer Protocol.
Data exchange
Like FTP and FTPS, SFTP follows a client-server architecture. In other words, in order to carry out an SFTP file transfer, you’ll need an SFTP client on one end and an SFTP server on the other end. SFTP servers listen on port 22 by default, and SFTP clients must establish connections with SFTP servers through that port. Once a connection is established, all commands, command responses and data (i.e., files) are sent through that single connection.
Firewall considerations
You won’t notice major differences between SFTP and FTPS in terms of data exchange usability or security capabilitiies. However, once you start configuring firewalls to support your file transfer connections, you’ll quickly realize how easier it is to work with SFTP than FTPS. Because SFTP only uses a single port and a single connection each time, firewall configurations are straightforward. To set up your firewall, you just need to know the port number your SFTP server is listening on — which, in most cases is port 22 — and open that port on your firewall.
Security features
As hinted earlier, SFTP and FTPS have similar security features. They both enable secure connections by enforcing data confidentiality, client and server authentication and data integrity. That being said, the underlying mechanisms that enable these capabilities differ. If you recall, FTPS derives its security features from SSL/TLS, whereas the SFTP protocol derives its features from SSH. Let’s go over those security features again.
- Data confidentiality: Also achieved through data-in-transit encryption. However, in this case, encryption is carried out through SSH instead of SSL/TLS.
- Client and server authentication: Achieved through pairs of public keys and private keys.
- Data integrity: Still uses mechanisms like HMAC, but delivered through SSH instead of SSL/TLS.
FTP vs. FTPS vs. SFTP comparison table
We only covered some of the key differences in the previous sections. Let’s cover more while placing each protocol side by side.
| Attributes | FTP | FTPS | SFTP |
| Cryptographic protocol | N/A | SSL/TLS | SSH |
| Default server port number | Command channel: 21 Data channel: depends on data connection mode used | Command channel: 21 Data channel: depends on data connection mode used | 22 |
| Authentication methods | Username and password | Username and password SSL/TLS certificates | Username and password SSH keys |
| Encryption | N/A | Always encrypts command channel. Optionally encrypts data channel. | Encrypts commands and data at all times |
| Data integrity | N/A | Provided by SSL/TLS | Provided by SSH |
| Firewall compatibility | Susceptible to firewall configuration issues due to differing characteristics of data connection modes | Susceptible to firewall configuration issues due to differing characteristics of data connection modes | Less prone to firewall configuration issues since only a single port is used |
| Transfer speed | Fastest of the three | As fast as SFTP but slower than FTP due to encryption functionality overhead | As fast as FTPS but slower than FTP due to encryption functionality overhead |
| Ease of setup | Easiest of the three | Digital certificate management can pose challenges | Public key/private key management can pose challenges |
| File management | Directory listing, file creation, file deletion and file rename | Directory listing, file creation, file deletion and file rename | Directory listing, file creation, file deletion and file rename |
| Platform compatibility | Readily available in older operating system (OS) versions. However, not as supported in newer versions due to security issues. | Easily integrated with FTP legacy systems and widely supported in Windows environments, but can be implemented differently to be even more compatible | Primarily designed for SSH-based environments like Linux, UNIX and macOS, which usually already have built-in support for SSH, but can be implemented differently to be even more compatible |
FTP vs. FTPS vs. SFTP use case comparisons
In case you’re finding it hard to determine appropriate use cases based on the information provided above, the following use case comparison table might help in that regard.
|
Use case |
FTP |
FTPS |
SFTP |
|
Internal/ intra-organizational file transfers |
Generally acceptable, except in organizations with strict security policies |
Ideal |
Ideal |
|
Website content management |
Commonly used, but not advisable if files contain sensitive data. |
Ideal |
Ideal |
|
Public file sharing |
Commonly used, but no longer suited for files containing confidential information |
Ideal |
Ideal |
|
Transfer of sensitive information |
Unacceptable |
Required |
Required |
|
Regulatory compliance |
Non-compliant |
Compliant |
Compliant |
|
Integration with legacy systems |
Most legacy systems readily provide FTP support |
Generally supported, except for much older systems that lack SSL/TLS support |
Limited support, unless the system already supports SSH v2. |
|
File backups |
Generally acceptable, except in organizations with strict security policies |
Ideal |
Ideal |
|
Large file transfers |
Commonly used, but not advisable if files contain sensitive data. |
Ideal |
Ideal |
|
User-initiated file transfers |
Generally acceptable, except in cases that involve sensitive data |
Ideal |
Ideal |
|
Business-to-Business (B2B) data exchanges |
Unacceptable |
Required |
Required |
|
One-time file transfers |
Generally acceptable, except in cases that involve sensitive data |
Ideal |
Ideal |
|
Cross-platform file sharing |
Commonly used, but no longer suited for data transfers involving confidential information |
Ideal, but can be challenging to implement |
Ideal, but can be challenging to implement |
|
Cloud-based file transfer |
Uncommon |
Uncommon |
Increasingly being supported |
Support FTP, FTPS and SFTP with a single solution
In many large organizations, it would be unrealistic to stick to just one file transfer protocol. Different trading partners and departments may have different protocol preferences. For instance, some might prefer SFTP, while others might require FTPS. Not only that, but some of your internal legacy systems may only support archaic protocols like FTP. Thus, it’s important to have the flexibility to support different protocols.
Traditionally, the way to do that would be to install software that supports a particular protocol. So, for instance, in the scenario described above, you would have to install an FTP server, an SFTP server, and an FTPS server. That wouldn’t be very efficient. It would also be very expensive and complicated from an administrative standpoint. A managed file transfer (MFT) solution would be a more cost-effective option.
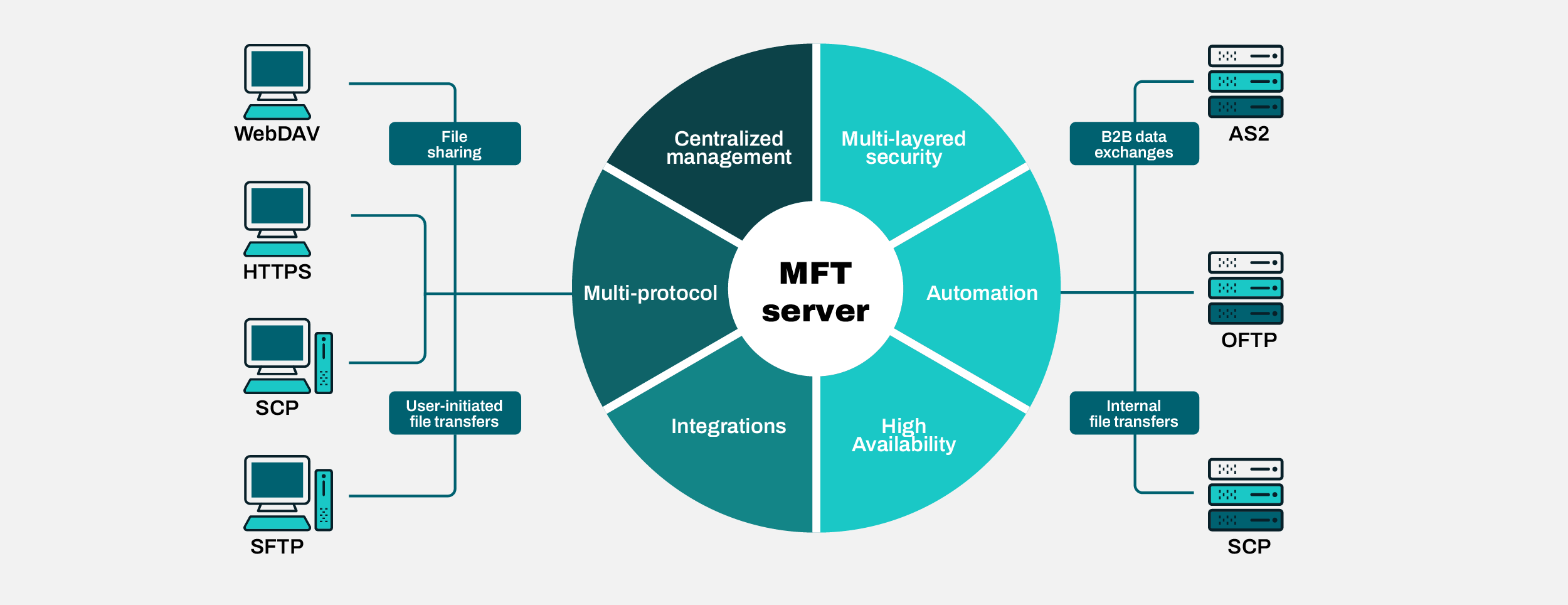
An MFT solution like JSCAPE can give you the optimal flexibility you need to interoperate with a wide range of file transfer systems, regardless of protocol, using a single solution. JSCAPE supports commonly used protocols, including FTP, FTPS, SFTP, SCP, HTTP, HTTPS, WebDAV, AS2, OFTP, TFTP and AFTP. It even allows you to transfer files with hosts that don’t have any file transfer service. Moreover, JSCAPE enables you to automate all your file transfer workflows without writing a single line of code.
Would you like to know more about JSCAPE? Schedule a quick demo now.
Frequently Asked Questions
What is FTP?
FTP (file transfer protocol) is a network protocol that has evolved over 40 years into RFC 959, which is the standard that FTP clients and servers follow today. The FTP protocol exchanges data using two separate channels known as the command channel and the data channel. When using FTP, both the command and data channels are unencrypted, and any data sent over these channels can be intercepted and read.
What is FTPS?
FTPS (FTP over secure sockets layer, or SSL) is a set of security extensions to create a more secure FTP protocol. When the FTP protocol was initially drafted 40 years ago, security wasn’t a concern. But now sending data over any public network without encryption is very risky and is prohibited by regulations like PCI-DSS and HIPAA. FTPS uses SSL and transport layer security (TLS) to secure data as it’s transferred. This encryption can be done manually, but it’s time-consuming and error-prone. Instead, many organizations use FTPS servers/FTPS clients to provide data security.
What is SFTP?
SSH File Transfer Protocol (SFTP) is often confused with FTPS, but they have nothing in common except their ability to securely transfer files. SFTP is actually based on the SSH (Secure Shell) protocol. Unlike FTPS, SFTP does not use separate command and data connections. Instead, both data and commands are transferred in specially formatted packets via a single connection. All data sent between client and server is encrypted using an agreed-upon encryption cipher. SFTP sessions can also be further protected through the use of public and private keys.

