Overview
Today, we’ll teach you how to set up a HTTPS to HTTP reverse proxy. This service can come in handy if you have an HTTP Web server hosted in an internal network that you would like external clients to access via HTTPS. That way, inbound clients connecting via the Internet can access your site securely.
What we want to do
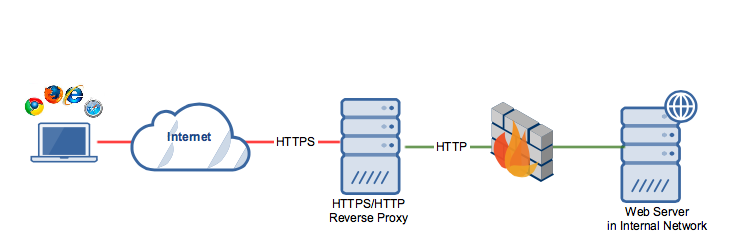
Notice that while the reverse proxy and web server exchange data via plain HTTP, clients connecting to the reverse proxy communicate over a secure HTTPS connection. As such, these connections are able to benefit from the security functions of SSL, such as data-in-transit encryption and host authentication.
This configuration makes perfect sense because, while client requests originating from the same internal network as the Web server can be considered safe, requests coming from the Internet should be treated with caution. If you’re curious about what this looks like in real-time, schedule a demo with one of our experts; they’d be happy to help.
How to Set-Up a HTTPS to HTTP Reverse Proxy
Then if you like what you see, simply download the free evaluation by clicking the download button at the end of the post.
Sounds good? Let’s proceed.
Launch the JSCAPE MFT Gateway Manager. It’s a Web GUI running on any popular browser, including Chrome, Firefox, Safari, and Internet Explorer.
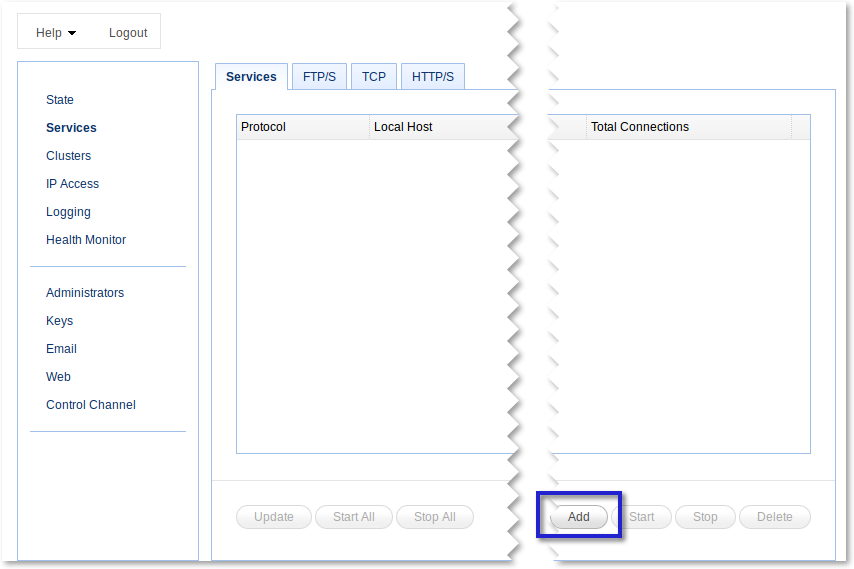
Once you’ve launched the Manager, navigate to the Services menu and click the Add button.
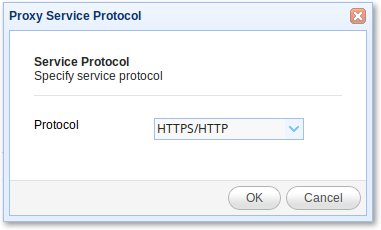
Select HTTPS/HTTP as the proxy service protocol from the Protocol drop-down list and click OK.
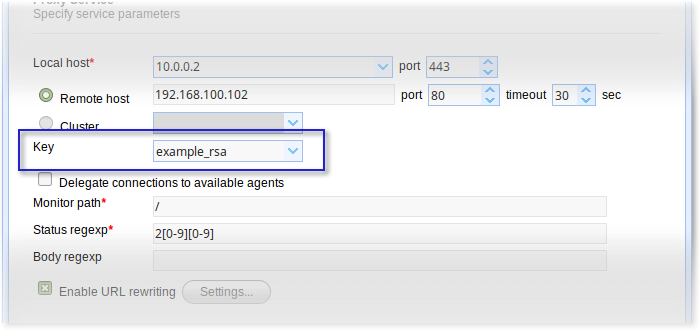
Enter the IP/host address of your reverse proxy. This will be the IP address/hostname your reverse proxy will be listening to and where external clients will connect via HTTPS. Also, specify the port number. The usual value is 443.
After that, specify the IP address/hostname of your HTTP server. This Web server would likely be found in your internal network, behind your corporate firewall. Also, specify the port number of that Web server. The usual value is 80.
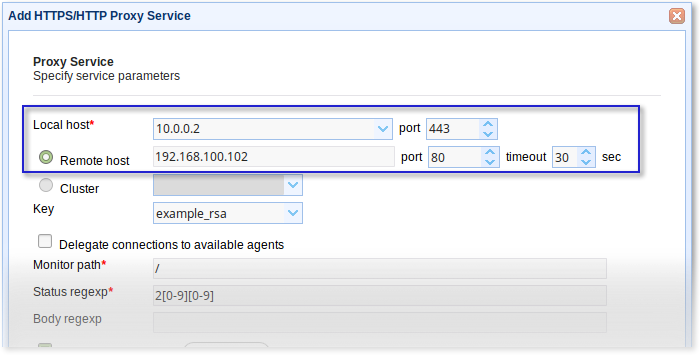
After that, go to the Key setting and select a server key. This is the key that will be used to provide data-in-motion encryption and server authentication.
Tick the Enable URL rewriting checkbox andclick the Settings button.
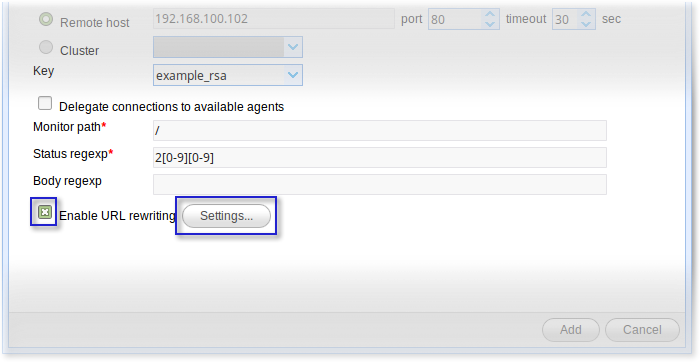
There can be instances when you may need to rewrite HTTP headers and/or content. For example, you might want to trap HTTP responses containing the target host/port and replace them with the local host/port of the gateway. This can be especially important in cases where HTML content returned by HTTP/S service contains relative and absolute URL references.
The URL rewrite rules will enable JSCAPE MFT Gateway to carry out those rewrites automatically.
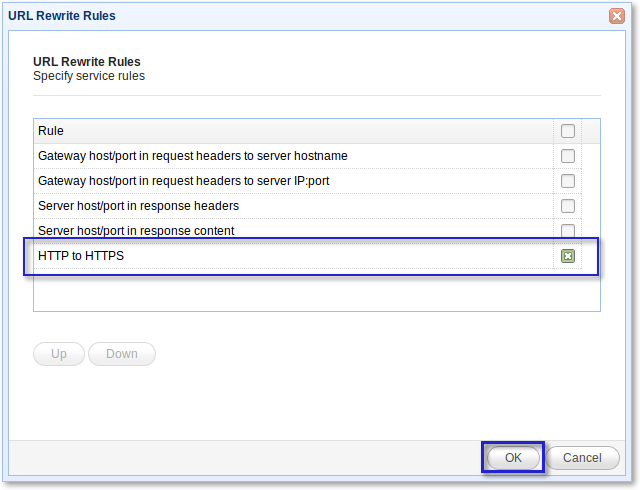
For more information about setting URL rewrite rules, click that link. But for now, tick HTTP to HTTPS and click OK.
Review your settings. If everything looks good, finalize this procedure by clicking the Add button.
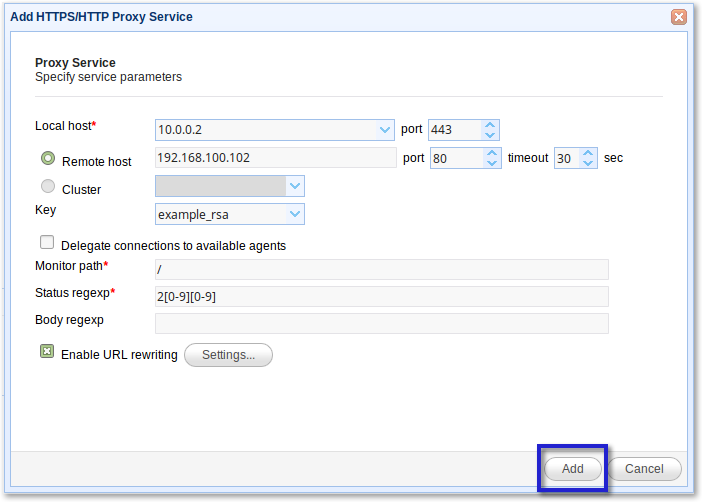
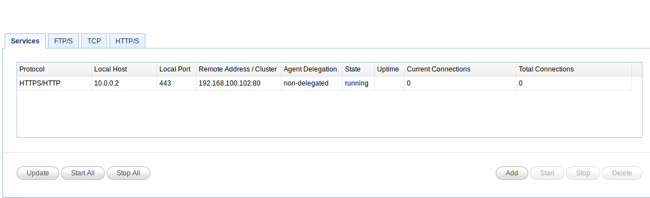
You should now see your HTTPS/HTTP service on the Services screen. Try connecting to it from a couple of Web clients.
Here’s a screenshot showing a Web browser connecting to a JSCAPE MFT Server Web-based file transfer service via the HTTPS/HTTP reverse proxy.

Get Started
Want to try setting up an HTTPS to HTTP Proxy Server yourself? Download the free, fully functional evaluation edition of JSCAPE MFT Gateway now.
Want to try setting up an HTTPS to HTTP Proxy Server yourself? Download the free, fully functional evaluation edition of JSCAPE MFT Gateway now.
Other articles related to this
Comparing Load Balancing Algorithms
Active-Active vs Active-Passive High Availability Cluster
Configuring A High Availability Cluster for Various TCP/UDP Services
How To Set Up SSL Client Authentication on an HTTPS and FTPS Server

