Overview
What is TFTP? Like its more popular and more versatile cousin, FTP, TFTP or Trivial File Transfer Protocol is also a protocol for transferring files. However, it’s targeted at certain tasks. In this post, you’ll learn about the basic properties of TFTP, where it’s commonly used, its vulnerabilities, how it differs from FTP, and other essential information about it.
Brief History and Basic Properties of Trivial File Transfer Protocol
TFTP runs over UDP (User Datagram Protocol) and uses port 69. It’s quite old but not nearly as old as FTP. First introduced in 1980 via IEN (Internet Experimental Note) 133, it was eventually defined the following year in RFC 783. The TFTP we know now is based on RFC 1350, which updated RFC 783 in 1992 and has in turn spawned a handful of updates, mostly specifying additional options for the blocksize, timeout interval, transfer size, and option negotiation. Links to those updates can be found on RFC 1350.
As the “trivial” part of its name suggests, TFTP is more like a stripped-down version of FTP (File Transfer Protocol), the ubiquitous protocol for sending files across a LAN or the Internet. Unlike FTP (and similar protocols like SFTP and FTPS), TFTP can’t let you: display a list of files in a directory, delete files, rename files, delete directories, and perform a few other actions that make FTP so versatile. It doesn’t even require user authentication. Generally speaking, TFTP can only perform two main tasks: write files and read files.
But that’s ok. The functionality it possesses is just right for the things it’s been designed to do; let’s walk through it with your account manager through your free trial.

Common uses
TFTP’s simple design and very minimal footprint makes it the ideal file transfer solution for the following tasks:
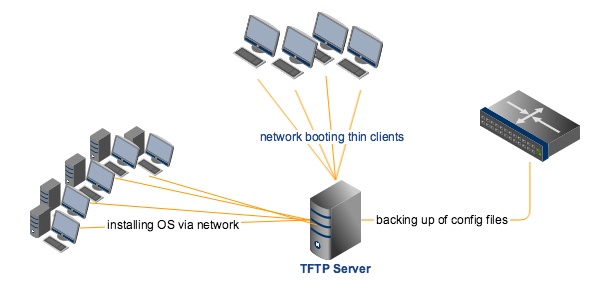
Network booting
Some devices, including diskless workstations, thin clients, and routers, can actually boot from the network instead of booting from a local hard drive. These devices have little use of local storage during normal operations and hence aren’t equipped with harddrives. They still need to boot up though, and a network boot via solutions like BOOTP, PXE, or BSDP offers the best alternative. Most of these use TFTP for distributing the needed boot file to the clients.
Because TFTP uses UDP, its relatively small protocol code (compared to say FTP’s) can be easily accommodated into the client’s ROM. As soon as the boot file, which may include the OS and the application needed by the client to perform its duties, has been downloaded via TFTP, the file will then be loaded unto the client’s RAM and will simply run from there.
Operating System network installations
Network booting likewise opens the doors to another cool activity – network-based installations! Major operating systems such as Windows, Linux, and Mac OS X, actually support network installations. That is, instead of using a DVD installer or a USB stick, you can simply connect the machine targeted for installation to your server and then perform the installation from there.
In a typical PXE boot install, for instance, TFTP is used for delivering the initial network bootstrap program (NBP), kernels, WinPE (for Windows installs), and other initial software to the clients. PXE installation is excellent for large networks where you can really see significant time-saving advantages over DVD-based or USB stick-based installations.
Upgrading IOS of Cisco appliances
TFTP server can play an important role when you upgrade the IOS of your Cisco appliances. First, it can be used for copying the startup configuration files and system image files to your TFTP server. Those copies can later be used as backups. And second, it can be used for copying the new system image itself from the server to the target Cisco appliance.
Backing up and retrieving configuration files of network devices
Other non-Cisco network devices (e.g. Dell PowerConnect, HP ProCurve, Juniper ScreenOS, 3COM, etc.) also allow you to backup their configuration files to a TFTP server.
Downloading executables to circuit boards
Several circuit boards allow you to download executables via TFTP.
Security concerns
TFTP’s simplicity has its downsides. Perhaps the most critical is its lack of security features. TFTP doesn’t have any built in encryption. It also does not support any client or server authentication function. Thus, for instance, nothing would prevent a hacker from spoofing your TFTP server, forcing your clients to reboot, and then compelling them to download configurations laced with malicious code.
However, in spite of its vulnerabilities, there is still no substitute for TFTP. There’s still no file transfer protocol out there that can perform the tasks TFTP is designed for, require less or the same amount of overhead, and provide better security. And even if an alternative comes along, the fact is, right now, TFTP is so widely used. It would take some time before it can be totally replaced.
Therefore, if you really need to implement TFTP in your organisation, you’ll have to take it upon yourself to mitigate the risks. For instance, you can restrict its use to private, local networks. You can also implement some kind of access control, e.g. limiting access to certain client IP addresses. If storing configuration files and other data in the clear is not acceptable to you, then you might also want to employ some kind of encryption on the server. You can write your own scripts to automate things or perform some system integration with other security solutions. Either that, or you can offer TFTP off of a secure file transfer server that already has several built-in security mechanisms.
Get Started
Looking to deploy TFTP on a secure file transfer server? Try JSCAPE MFT Server. It supports TFTP as well as other file tansfer protocols, including FTP, SFTP, FTPS, AS2, OFTP, WebDAV, AFTP, and others. If you want to give it a try, request your free trial now.

