Overview
SFTP is a secure method for transferring files between two computers. SFTP can stand for either SSH File Transfer Protocol or Secure File Transfer Protocol. This post will introduce you to the major functions of SFTP, its differences and similarities with FTP, its basic usage, and other important characteristics.
Main functions of SFTP
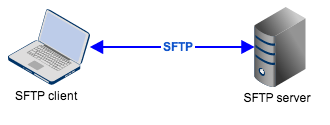
SFTP is primarily used for uploading or downloading files between a local computer and a remote one. The remote computer can be located in another building, city, or even in another continent across the globe. SFTP file transfers can be carried out between a client (controlled by a user) and a server.
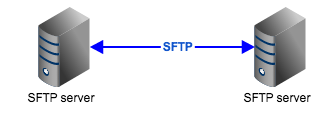
They can also be carried out between two servers through what is known as a server to server file transfer.
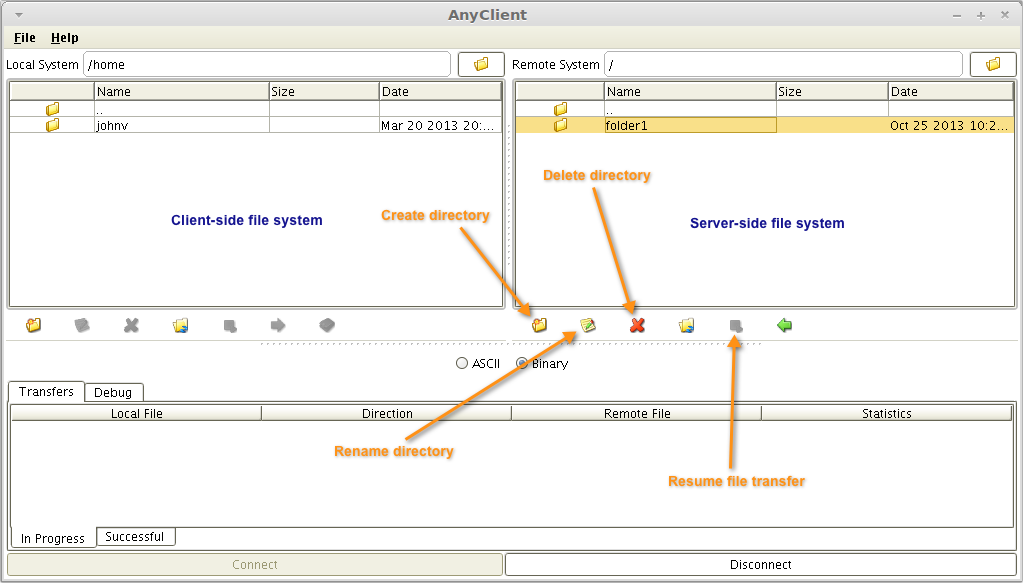
But SFTP isn’t just for transferring files per se. By using an SFTP client, a user can list directory contents to view files and subdirectories, create new directories, rename directories, and even delete files and directories.
The right panel in the screenshot below shows an SFTP server’s filesystem as viewed from AnyClient, a graphical multi-protocol file transfer client that also supports SFTP. Notice that this SFTP client’s GUI also has a Resume button. That’s because SFTP file transfers can actually be resumed if ever they are interrupted in the middle of a transfer.
SFTP vs FTP
SFTP’s major functionalities (i.e., directory listings, directory creation, and directory and file removals) are also characteristics of FTP. But in spite of their similarities both in major functionalities and acronyms, SFTP and FTP are really two distinct protocols. Unlike FTPS (FTP-SSL), which is really an extension of FTP, SFTP is actually an extension of another technology named SSH.
SSH (Secure Shell) is mainly a method used for establishing a secure network connection with another computer (mostly UNIX-based) and allow the user to issue commands remotely. SFTP, along with other protocols like SCP and FISH, was developed to provide a mechanism for transferring files over SSH.
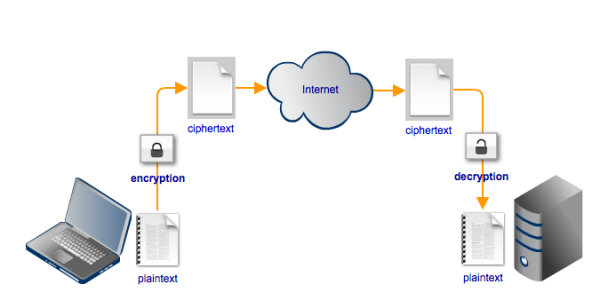
SSH, and consequently SFTP, secures its connection through encryption, which renders data unreadable by substituting the original content (known as plaintext) with an incomprehensible string of characters (known as ciphertext).
Only the person (or machine) who has the required decryption key can convert the ciphertext back into its original form. Normally, in the context of an SFTP file transfer, that person would be the recipient of the file being sent. Thus, if a file is sent via SFTP, its contents cannot be viewed by anyone who attempts to eavesdrop on the file transfer session.
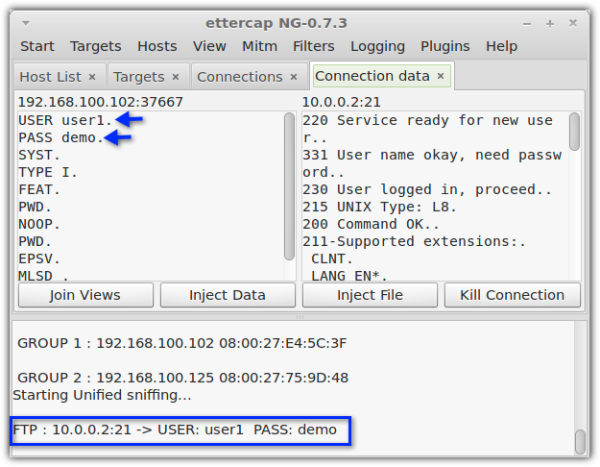
Let me show you how an FTP connection would look like from an eavesdropper’s hacking tool. FTP doesn’t support encryption. It can only transmit files in plaintext. Notice how visible the username and password can be because of that. Once the eavesdropper gets a hold of those login credentials, he can use them to gain access into the server at a later time and do what ever he wishes with the files stored under that user’s account.
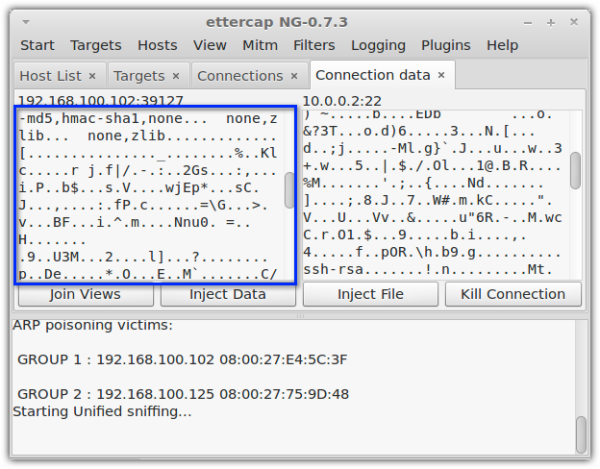
Now, here’s how an SFTP connection would look like from the same tool. The eavesdropper wouldn’t be able to obtain any information from that.
Encryption isn’t the only security mechanism supported by SFTP. SFTP also features public key authentication, which adds a layer of authentication to the usual username/password. In public key authentication, users are issued what are known as private keys. These are unique files which users submit to the server during login. Only if the server recognizes the private key as one of its keys will the user be granted access.
The video Public Key Authentication in SFTP/SSH with JSCAPE MFT Server details all the necessary steps for setting up public key authentication on the server and for implementing it on the client side.
The SFTP port
Because SFTP and FTPS provide similar secure file transfer features (both support encryption and some form of public key authentication – FTPS uses SSL certificates), they are often pitted against each other. One advantage SFTP has over FTPS is its use of a single port, usually port 22.
FTPS, being an extension of FTP, uses two ports: one port for its command channel (usually port 21) and another for its data channel. The data channel port is usually randomly selected from a range of ports, which presents issues when setting up firewalls and port forwarding. For more details regarding this problem, please read the article Active vs Passive FTP Simplified.
Since SFTP only uses one port, it’s much easier to integrate it into your firewall settings. This single port supports all the information exchanged throughout an entire SFTP connection, including authentication, commands, and data.
To learn more about the key differences between SFTP, FTPS and FTP, please click that link.
How to use SFTP
As mentioned earlier, SFTP can be implemented in either a client-server or a server-server configuration.
To implement a client-server configuration, users would need an SFTP client for initiating the file transfers and an SFTP server to connect to. One example of an SFTP server is JSCAPE MFT Server, a multi-platform and multi-protocol secure file transfer server that supports SFTP and a host of other file transfer protocols like FTP, FTPS, WebDAV and others.
To set up a server-server configuration for SFTP, you would need two SFTP-enabled servers. This is slightly more sophisticated than a client-server configuration but is the recommended configuration for enterprise-grade file transfers. If you have a need for it in your business operations, the article How To Set Up a Server To Server File Transfer should give you enough information for setting up an SFTP server-to-server file transfer.
Where to go from here
You can give SFTP a test drive using AnyClient and JSCAPE MFT Server. AnyClient is totally free, while JSCAPE MFT Server comes with a free, fully-functional evaluation edition. Download them now.
Download the always free AnyClient Now
Download JSCAPE MFT Server Trial

