Protecting Your File Transfer Service from Internal Threats

Overview
[Last updated: December 2020] Malicious insiders and careless insiders are increasingly posing serious risks to file transfer systems. If nothing is done to mitigate them, these internal threats can cause data loss or, worse, massive penalty-inducing data breaches. In this post, we take a closer look at internal threats, how they put file transfer systems at risk, and what you can do to mitigate them.

Alarming statistics on internal threats
Before we proceed with a discussion on how internal threats impact file transfer systems, let me share with you some relevant highlights about internal or insider threats from Ponemen's 9th annual Cost of Cybercrime study:
-
The cost of malicious insider attacks has grown by 15% over the last year, which is the second fastest growing cost among all types of cyber attacks.
-
The cost of malicious insider attacks is now at an annual average of $1.6 million per organization;
-
Executives polled in the Accenture 2018 State of Cyber Resilience survey identified the accidental publication of confidential information by employees and insider attacks as having the second greatest impact in causing a data breach in their organizations.
What you need to know about internal threats
It is easy to see why internal threats can inflict greater harm to a company. Compared to outsiders, we normally impart a higher level of trust to people who we regularly come in contact with in the workplace, such as colleagues, employees, contractors, technicians, consultants, and trading partners.
That is why we spend so much on security solutions like firewalls, reverse proxies, and Intrusion Detection and Prevention Systems, that are primarily designed to thwart external threats. We focus too much on keeping external threats out, that we leave ourselves vulnerable within.
But let me ask you this. What makes you think these insiders will never turn against you, when there are actually quite a number of things that can motivate them to do so? Allow me to mention a few:
The perception of having been treated unfairly
This is actually very common. Disgruntled employees who leave your organization, whether through their own volition or through dismissal, may want to get back at your company by either stealing sensitive information and then handing them over to competitors or simply sabotaging your systems.
Corporate espionage
Other malicious insiders don't have to feel unjustly treated to be tempted into divulging confidential information to your competitors. The thought of getting rich quick or overcoming a personal financial crisis can be enough motivation for some people to disclose secret formulas, employee salaries, supplier information, or other company secrets to your competitors.
Allure of the black market
Competitors aren't the only entities interested in the kind of information insiders have access to. Some of your files can contain a sizeable amount of employee or customer personal data that can fetch a hefty price in the black market.
Remember that insiders not only know the intricacies of your systems, they also have easy access to them. Once they've developed a motive, it would be easy for these individuals to carry out their malicious intentions.
So what has all these got to do with file transfers?
Insider threats to file transfers
File transfer servers may attract malevolent insiders because of two reasons:
-
File transfer servers normally receive a large number of files on a daily basis. Some of these files contain sensitive data.
-
Commonly used file transfer systems (usually FTP servers) are grossly insecure.
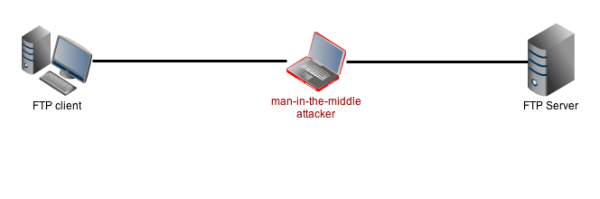
Data-in-transit and man-in-the-middle attacks
Nefarious individuals can steal sensitive data from your file transfer systems by attacking either one of two areas: the network through which your transmitted files traverse or your server's storage devices themselves.
Data-in-transit is usually compromised through a man-in-the-middle attack using a sniffer like Ettercap, NAI Sniffer, Wireshark, or TCPDump.
Here's a post that contains a more thorough discussion on sniffing, man-in-the-middle-attacks, and data-in-motion encryption. It also include excerpts of a demo where I compared sniffing results on an FTP connection and FTPS and SFTP connections, so you might want to check that out after this article.
In the meantime, let me just say that a man-in-the-middle attack can enable an attacker to acquire a user's username and password if the user is using an insecure protocol like FTP, which unfortunately carries these login credentials in plaintext.
Sniffers like Ettercap are best employed in a LAN because they have to be a part of the same network as the target machines to be effective. Suffice to say, it would be much easier to use them and launch MiTM attacks from within your network. Hence, it wouldn't be surprising for a man-in-the-middle-attack to be carried out by someone who has access to your internal network.
Viruses
Viruses are another serious threat to file transfer systems. Once an infected file gets uploaded to your server, it can infect the files there. And then when infected files are downloaded from the server, the infection can spread to client machines as well.
The thing about viruses is that they don't always have to be uploaded by nefarious individuals. Infected files can also be inadvertently uploaded unknowingly by innocent insiders.
Careless insiders
Sometimes, insiders themselves don't need the motivation to perform malicious acts in order for those acts to be carried out. Nefarious individuals (whether outsiders or insiders) can exploit vulnerabilities caused by employees who don't handle confidential data properly or don't follow security policies.
Communicating or sharing data over non-secure channels, writing usernames and passwords on post-its and sticking them conspicuously on desktops, or even using easy-to-guess passwords are just some of the common practices that can provide attackers an opening to your systems.
Countermeasures for protecting file transfers
Let's now take a look at some of the countermeasures you can implement to protect your file transfer system.
Use secure file transfer protocols
A truly secure file transfer protocol is one that can prevent attackers from viewing any sensitive information transmitted during a file transfer session, such as usernames and passwords. Plain FTP is already out because it transmits usernames and passwords in plaintext. Better alternatives to FTP are FTPS and SFTP, which both encrypt data during transmission. Click the following link to understand the key differences between FTP, FTPS, and SFTP.
Employ antivirus software
The best way to prevent a virus infection in your server is by using an antivirus. However, since most file transfer solutions don't have built-in antivirus protection, it's best to pick a solution that integrates with well-established antivirus applications. There are two ways to go about with this. One is by integrating with a locally-installed antivirus solution. Another is by offloading virus scanning to a separate solution like an ICAP AV server.
Here are two articles that discuss these two different approaches:
Perform Directory Virus Scan Using Kaspersky
What ICAP Antivirus Scanning Means for Your File Transfers
Implement strict password policies
Usernames/password authentication is the most common form of access control mechanism. Since they are often the only keys to your system, it is important to make sure they function as they should. Weak passwords or passwords that have been in use since forever won't be able to withstand the onslaught of a skilled and determined attacker.
I suggest you adopt the password requirements of PCI-DSS. It's a very comprehensive list of password policies. Click that link to learn more about it.
Apply two-factor or multi-factor authentication
Passwords, no matter how strong, aren't 100% secure. Even the strongest passwords can be acquired through non-brute force cyber attacks like social engineering or phishing. One way to prevent unauthorized logins due to stolen passwords is to apply 2-factor authentication (2FA). With 2FA, it won't be enough for an attacker to acquire a user's password to break into that user's account.
Encrypt data stored in your server
Attackers may also attempt to acquire files stored in your file transfer server. To prevent them from getting any valuable information, protect your files with data-at-rest encryption such as OpenPGP. Data-at-rest encryption can prevent files from being compromised even if the attacker is able to physically acquire the hard disks of your server.
Summary
The countermeasures we just mentioned can already go a long way in protecting your file transfer system from internal threats. All those countermeasures are found in JSCAPE MFT Server, a managed file transfer server that supports a wide range of secure file transfer protocols as well as a host of other security measures.