Despite FTP’s vulnerabilities, many Windows users still use FTP clients for transferring files over the Internet. If you really have to keep using that archaic file transfer protocol, at least do it securely. Here’s what we suggest when using a Windows FTP Client for secure downloads.
Why do you need to secure FTP?
FTP is no longer recommended for transferring files, especially if the file transfer is carried out over the Internet. FTP transmits files in plaintext, making it vulnerable to network-based attacks. It’s fairly easy to carry out a man-in-the-middle attack on an FTP connection. All you need is a packet sniffer and some eavesdropping skills to grab information like usernames and passwords from FTP connections.
Because of its vulnerabilities, the use of FTP is now prohibited by data security/privacy laws and regulations like HIPAA and PCI DSS. To protect senstive information while in transit, these laws require data transfers to be secured by data-in-motion encryption.
Options for data in motion encryption
Encryption is a mechanism that renders data unreadable. Data-in-motion encryption, on the other hand, refers to a form of encryption that encrypts data as it traverses a network. This prevents eavesdroppers from understanding any information carried by the transmitted file.
There are several ways of achieving data-in-motion encryption. The common practice is to replace FTP (and other unencrypted network protocols) with secure file transfer protocols like FTPS and SFTP. These protocols already come with built-in encryption mechanisms that can counter eavesdroppers.
But what if you really want to use FTP and still want to preserve data confidentiality during transmissions? Well, there’s another option. It’s slightly more complicated than just using secure file transfer protocols. But it works, so you might want to check it out.
What you can do is secure the file with a file encryption tool before sending it out. That way, it will be encrypted while being transmitted through FTP. One solution that allows you to do this is OpenPGP. OpenPGP is a standard currently specified in RFC 4880. Programs adhering to this standard can be used for encrypting files, texts, emails, directories, and even whole disk partitions.
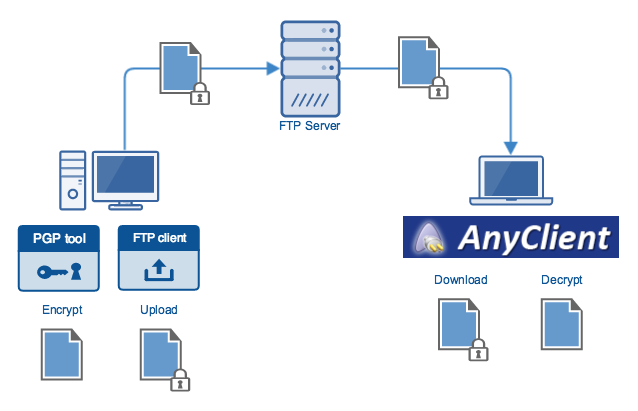
When using PGP, the file will have to be encrypted through a separate tool before it’s uploaded through a Windows FTP client. So even if the file will still be sent over FTP, it will already be in encrypted form. Of course, for this file to be readable to the recipient, the recipient should have a way of decrypting it. Normally, as with the encryption process, decryption is done using a separate tool.
To illustrate:

A Windows FTP client that decrypts a PGP-encrypted file
Having separate tools for encryption/decryption and uploads/downloads complicates things. But there’s a way to simplify the decryption part. You can use AnyClient. It’s a free file transfer client that runs on Windows and other operating systems. The great thing about AnyClient is that it already has a built-in PGP-decryption tool.
This combines the download-decryption two-step process into one.
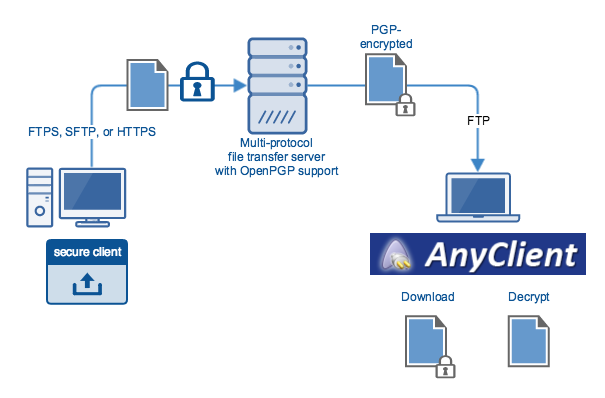
AnyClient’s auto-decryption feature can also be useful in this scenario:
A file uploaded using an encrypted file transfer protocol like FTPS, SFTP, or HTTPS, auto-encrypted with OpenPGP on the server, and then downloaded over FTP using AnyClient. The upload doesn’t have to be PGP-encrypted since those secure file transfer protocols already support data-in-motion encryption. The downloaded, however, which will be carried out over FTP, has to be PGP-encrypted.
However, for this to work, you would have to use a server that:
Once the file has been PGP-encrypted on the server, a Windows user armed with AnyClient can then download it securely over FTP.
How to set things up
First, download our ftp client, AnyClient. This Windows FTP client is totally free, so go ahead and download it now.
Download the always free AnyClientNow
Next, read this tutorial:
Automatically PGP Decrypt Files Upon Download from FTP Server
Other posts you might also want to read
Countering Packet Sniffers Using Encrypted FTP

