Last week, we published the blog post ‘The Ultimate Guide To Hardening Your Secure File Transfer Server‘, where we shared several tips on how you could take advantage of the large selection of file transfer security features on JSCAPE MFT Server.
Although that article was pretty exhaustive, there’s still so much you can do to further secure this managed file transfer solution. That’s simply because MFT Server is just packed with so many security features. And so, there’s so much to discuss in as far as security is concerned.
This inspired us to come up with a series of short blog posts accompanied by an equally short video. The idea is to share with you bite-sized security tips that you can quickly digest in just a minute or two. It won’t eat up much of your time, but in that very short period, you would have already gained valuable information that you can later on apply to improve the security of your file transfer server.
Let’s proceed with the first tip.
Play this if you want to watch the video version
For today’s security tip, we talk about disabling plain FTP. The reason you would want to disable plain FTP on your file transfer server is because it transmits data in plaintext. That means, the transmission can be intercepted by a packet sniffer, and whoever is using that packet sniffer can easily obtain sensitive information like the user’s username and password.
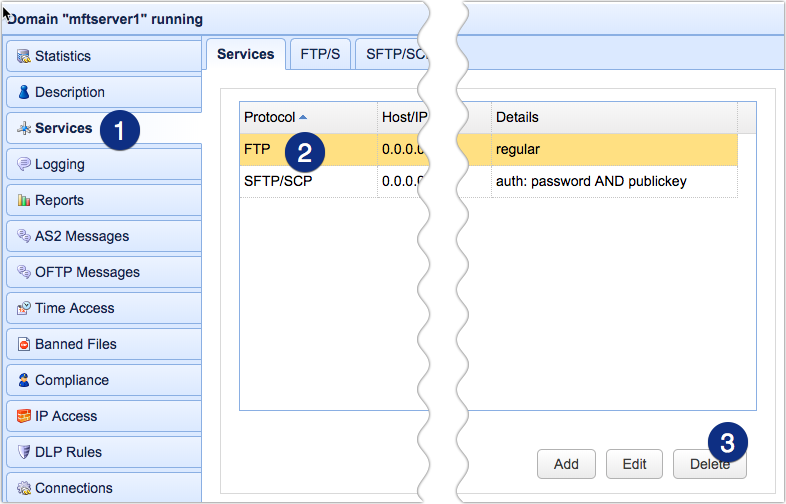
This vulnerability in FTP is the reason why this protocol is prohibited by data protection and security laws and regulations like HIPAA and PCI-DSS. So, to disable plain FTP on JSCAPE MFT Server, navigate into a domain (you might have to do this in all of your domains if you have more than one), go to the Services module and look for the FTP service.
You can then either delete that service…
or edit it, and then make sure the type is set to explicit SSL, forced explicit SSL, or implicit SSL.
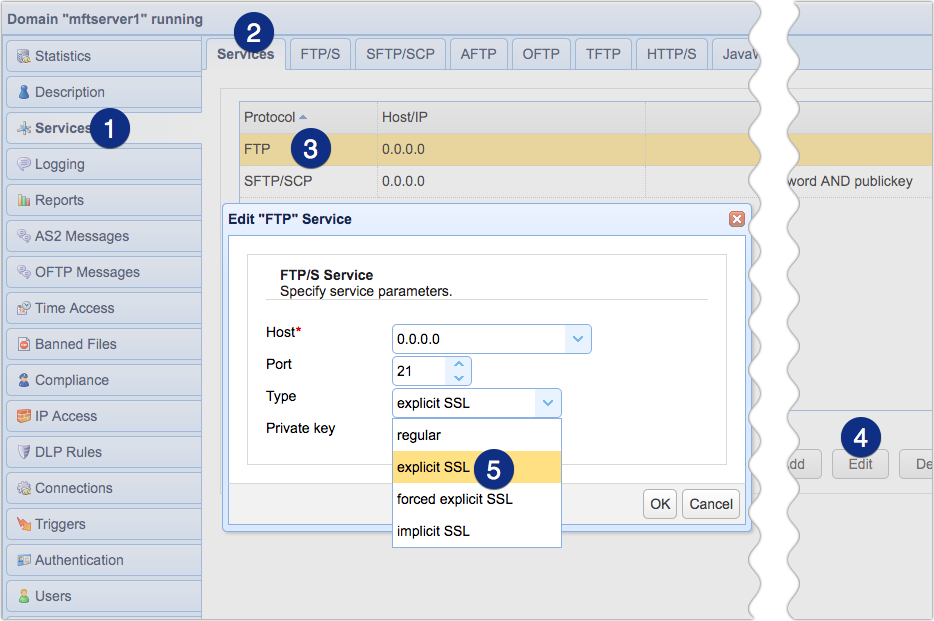
Note however, if you disable plain FTP, clients who are used to connecting through that protocol might not be able to connect. So, you should inform your users and trading partners and advise them to connect through FTPS or some other secure file transfer protocol (e.g. SFTP or HTTPS). Of course, you need to enable that protocol on your MFT Server.
That’s it. See you again next time for another MFT security tip.



