Overview
JSCAPE MFT Server has a reverse proxy feature that allows you to map it to a user’s or group’s virtual path. This can come in handy when you want to transparently provide users access to one or more remote services through a single account. JSCAPE MFT Server‘s reverse proxy supports several file transfer protocols. But today, we’ll just focus on configuring a SFTP reverse proxy.
What we’re trying to achieve
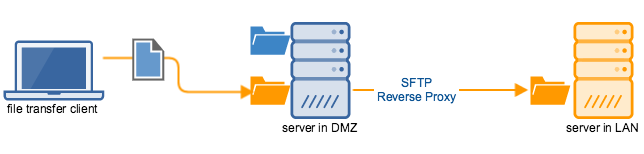
Let me explain what we’re trying to achieve. Let’s say you have two servers. One server is in your DMZ and the other one is in your LAN. One of the folders on your DMZ server is mapped to a SFTP reverse proxy that points to a folder on your LAN server.
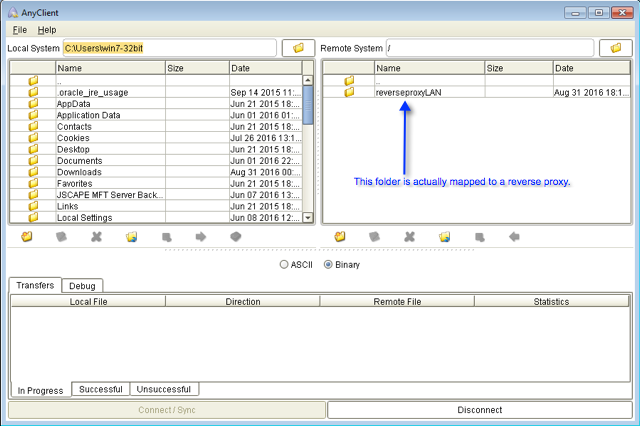
So when a user (who has sufficient access rights to the mapped folder) logs in to your DMZ server, perhaps through FTP, FTPS, SFTP or some other file transfer protocol, that user will see that mapped folder (see screenshot below) and be able to upload files to it. Those files that he uploads to that mapped folder won’t be stored on the DMZ server. Instead, they’ll be forwarded to the LAN server.
Note that the user doesn’t have to log in directly to the LAN server. All the user has to do is log in to the DMZ server and he’ll instantly have access to the LAN server’s SFTP service. In effect, this reverse proxy will allow your users to access both the services on the DMZ server and one or more remote services (you can add more reverse proxy services) by just using a single account.
Setting up the SFTP reverse proxy
Let’s now go through the steps of setting up that SFTP reverse proxy. We’ll be configuring settings in two places, the server on the DMZ and the server on the LAN. Let’s start with the server on the DMZ.
On the DMZ server
In order to achieve what we want using the instructions outlined below, your DMZ server must be running an instance of JSCAPE MFT Server.
Generate a client key and export its public key
The first thing we need to do is generate a Client Key. We’ll be using this key to authenticate to our LAN server using public key authentication. If you just want to use password authentication, you may go straight to the section “Add a SFTP reverse proxy“.
Login to JSCAPE MFT Server and then go to Server > Key Manager > Client Keys. Click the Generate button. Follow the instructions on the screen to generate a public-private client key pair.
You can use the article “2 Ways to Generate an SFTP Private Key” for reference. Go straight to the section “1. Obtaining an SFTP private key via the Key Manager” in that article.
Make sure you save the Private Key File in PEM format and take note of the password.
Once you’re back at the main screen, select the newly generated Client Key and export its public key.
Read the section “Step 2: Exporting the public key file” of the article “Setting Up Public Key Authentication Between Trading Partners” for more details.
On the LAN server
The next step would be to import the exported public key into the LAN server. The way you do this would vary from one server to another. But if you’re also using JSCAPE MFT Server for your LAN server, this is how you’d do it. Login to the LAN server and go to Server > Key Manager > Client Keys. Import the public key you exported earlier. Give this key an alias. For example, “user1guestkey”.
Go to Home and navigate into your desired domain. Assign the Client Key (in our case, “user1guestkey”) to an existing user account. For example, the user account is “user1guest”
You may read the section “Step 3: Importing the public key file into the trading partner’s server” of the article”Setting Up Public Key Authentication Between Trading Partners” for reference.
The instructions in that article refer to a “trading partner” but the instructions are the same for our LAN server. Once you’ve completed the key importation process, go back to your DMZ server.
On the DMZ server
Add a SFTP Reverse Proxy
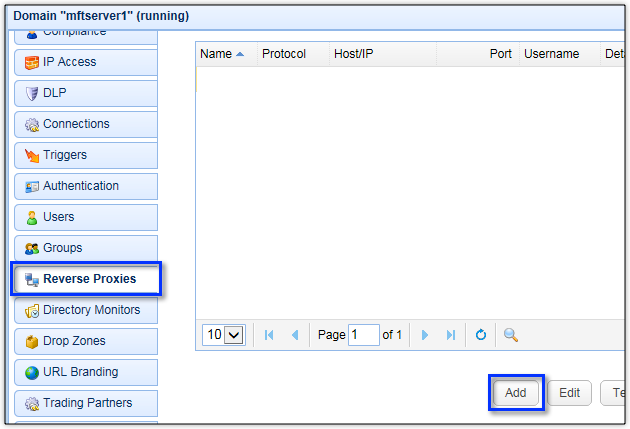
Navigate into your desired domain and go to Reverse Proxies.
Click the Add button to add a new reverse proxy.
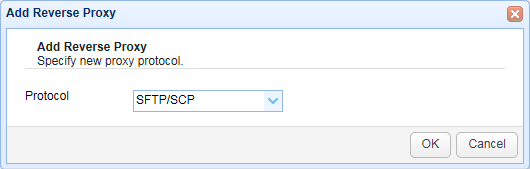
Select SFTP/SCP for the protocol and click OK.
You’ll then be asked to specify the SFTP reverse proxy settings.
Give the proxy a name, e.g. “LAN server”.
Enter the Host/IP of the LAN server.
Select the “Enter credentials” option button.
Leave the Password field blank. If you’re using password authentication instead of public key authentication, then enter the corresponding password in this field.
In the Key File field, browse to the private key file that was generated earlier. Enter the Private Key File’s corresponding password.
Click Test Server to test the connection. If all goes well, you should now have successfully configured your SFTP reverse proxy.
Get started
Want to try this out? Download the free, fully-functional evaluation edition of JSCAPE MFT Server.
Download JSCAPE MFT Server Trial

