A Guide to HIPAA Compliant File Transfers - Part 1 | JSCAPE

For some entities in the health care industry, file transfer activities are no longer as simple as before. Measures have to be taken to make sure violations aren't made against HIPAA. FTP services, perhaps the most widely used services for transferring large files over the Internet, now require enhancements to ensure that data considered as electronic protected health information (ePHI) are protected throughout an FTP transfer.
Entities covered by HIPAA include:
- Health plans(e.g. , Medical, Dental, and Vision Plans, HMOs, Medicare and Medicaid, most Long-Term Care Insurers, Veterans Health Plans, and certain Company Health Plans)
- Health care clearinghouses- These are companies who convert nonstandard health information into standard form or vice versa (e.g. billing services, repricing companies, value-added networks, and community health management information systems)
- Health care providers(e.g. doctors, clinics, dentists, nursing homes, pharmacies, psychologists and chiropractors) who transmit health information electronically.
So if your organization falls into any of these categories and file transfers are part of your usual activities, then this article's for you and you should request a free trial of JSCAPE.
In this article, I've put together 5 steps that will help you carry out HIPAA compliant secure file transfers. But before that, I'll start by giving you a brief discussion on HIPAA. In particular, I'll show you where the provisions that affect file transfers can be found. I'll then trace down to the corresponding regulation as well as the specific requirements comprising it that directly affect file transfers.
Provisions in HIPAA affecting file transfers
The full HIPAA (Health Insurance Portability and Accountability Act) law is actually made up of two main parts:
Title I - Health Care Access, Portability, and Renewability
and
Title II - Preventing Health Care Fraud and Abuse; Administrative Simplification; Medical Liability Reform
However, it is the requirements set forth in Title II - particularly subtitle F, sections 261 through 264 - that really call for the adoption of standards that have an effect on file transfers.
These requirements fall under the Administrative Simplification provisions of HIPAA, which Congress passed in order to protect the privacy and security of ePHI while in the possession of HIPAA-covered entities or when they are being transmitted either from one covered entity to another or from a covered entity to a non-covered entity. In addition, these requirements are also aimed at enhancing efficiency in the health care industry through the use of standardized electronic transactions.
The body tasked to come up with such standards, which is also specified in HIPAA's Administrative Simplification provisions, is the Department of Health and Human Services (HHS).In turn, the HHS came up with rules implementing those provisions. These rules include:
- the Privacy Rule,
- the Electronic Transactions and Code Sets Rule,
- the National identifier requirements for employers, providers, and health plans, and
- the Security Rule
A detailed discussion on the Electronic Transactions Rule as it relates to data/file transfers can be found in the article Securing HIPAA EDI Transactions with AS2.
This 3-part article focuses on the Security Rule, for it contains the Technical Safeguards, the set of standards that deal with automated processes used in protecting data as well as controlling access to those data. The Security Rule, which is documented in 45 CFR (Code of Federal Regulations) Part 160 and Part 164, Subparts A and C, is designed to address vulnerabilities arising from technological advancements in the health care industry and from the rapidly growing volume of ePHI.
In other words, it applies to computers, information systems, electronic health records (EHR), computerized physician order entry (CPOE), clinical software applications, and many others, including file transfer services. Other sets of standards that belong to the Security Rule are the Administrative Safeguards and Physical Safeguards.
Administrative Safeguards is composed of those standards that deal with administrative functions such as assignment or delegation of security responsibilities as well as security training activities. On the other hand, Physical Safeguards, deal with mechanisms for protecting electronic systems, equipment, and the data they hold from various threats.
You will have to be familiar with all three safeguards to ensure comprehensive HIPAA compliance. I suggest you check out the Security Rule Guidance material found in the HHS website after reading this article.
To illustrate what we've taken up so far:
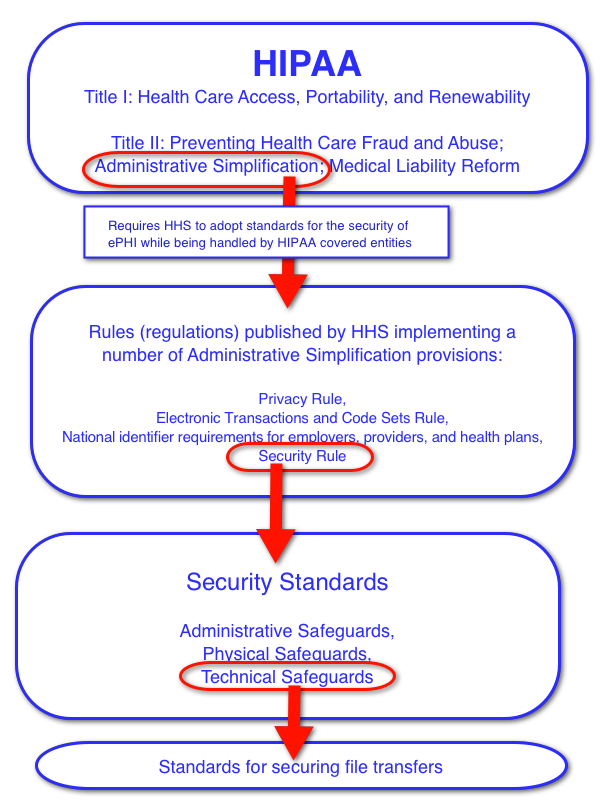
What I have drawn up here is a sort of reference guide that will help you find the most relevant information found in the HIPAA law itself and its corresponding regulation. This will streamline your research work as you seek legal footing before moving forward in your HIPAA file transfer compliance initiatives.
In Part 2 of this post, I'll zoom in on the specific HIPAA standards that impact file transfers. I hope to see you there then.