Using DLP to Protect Credit Card Data - Part 2

If you followed the steps in Part 1, then you should now have a DLP-enabled group. That group directory will have the capability to detect files stored in it that contain certain credit card numbers. If a member of that group attempts to download such a file, the server will prevent the download from taking place and fire a "DLP rule matched" event. In the screenshot below, a user is prevented by JSCAPE's DLP from downloading a file containing MasterCard numbers.
Here in Part 2, we're going to show you how to catch that event and perform certain trigger actions off of it.
If you prefer to watch a video version of this blog post, click play below. Otherwise, just proceed.
Being able to prevent group members from downloading files that they shouldn't have access to is already a step in the right direction in terms of securing files in your managed file transfer server. But we won't stop there. In our succeeding discussions, you'll also learn how to:
-
Send an email notification (presumably to a system administrator) warning that credit card information may have been detected in the group directory question, and
-
Render the file unreadable using OpenPGP encryption.
Remember in Part 1, we chose "deny all" when setting the Access level. That setting is the reason why the download shown in the screenshot above was not allowed to push through.
Are all these actions of notifying, encrypting, and denying access absolutely necessary? Maybe not. But if your company is covered by regulations like PCI DSS, then they probably are. PCI DSS has certain requirements that specify where credit card information should be stored and who should have access to them.
Recommended read: Guide To PCI DSS Compliant File Transfers
If the group in question is not authorized to view such information, then the file containing the credit card information is certainly in the wrong place and something has to be done about it immediately.
Sending an email that credit card information may have been detected
Here's how you set JSCAPE MFT Server to automatically send an email once a DLP rule match occurs.

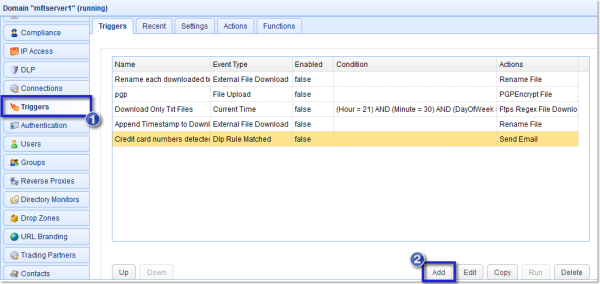
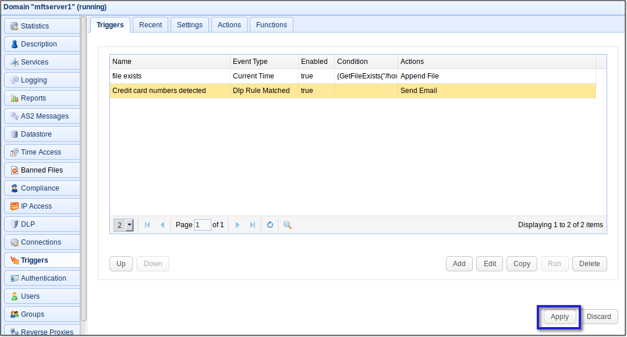
Go to the Triggers node and click the Add button.
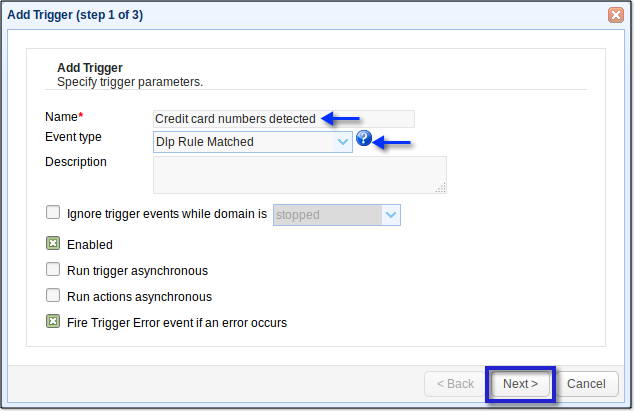
Give the trigger a descriptive name and choose DLP Rule Matched from the Event Type drop-down list. Click Next.
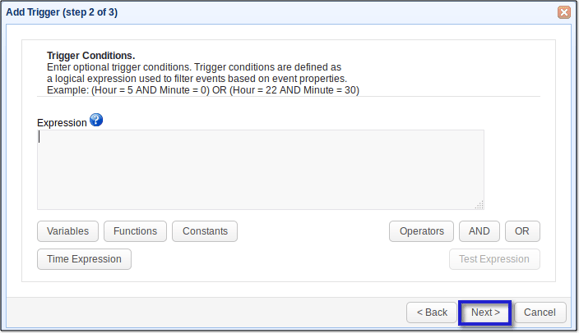
Click Next.
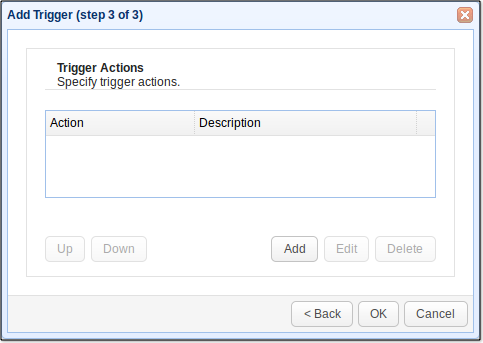
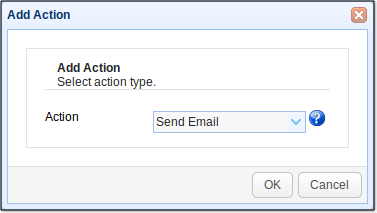
Click Add.
Select Send Email from the Action drop-down list and then click OK.
In the next screen, enter information pertinent to the sender's email account like the Hostname, Port, Connection Type, Username, and Password. The values you enter into the Hostname, Port, and Connection Type will depend on the email hosting service. What you see here is for Gmail. Enter the sender's email into the From field and the recipient's email into the To field.
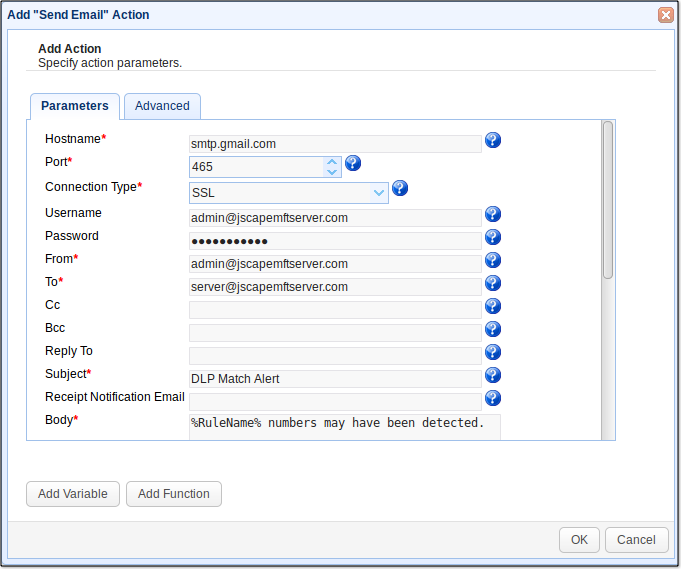
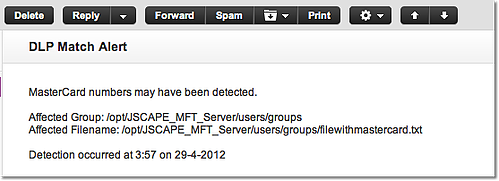
Enter a descriptive Subject (e.g. DLP Match Alert) and then add more details regarding the incident into the Body. Here's what we used for our Body:
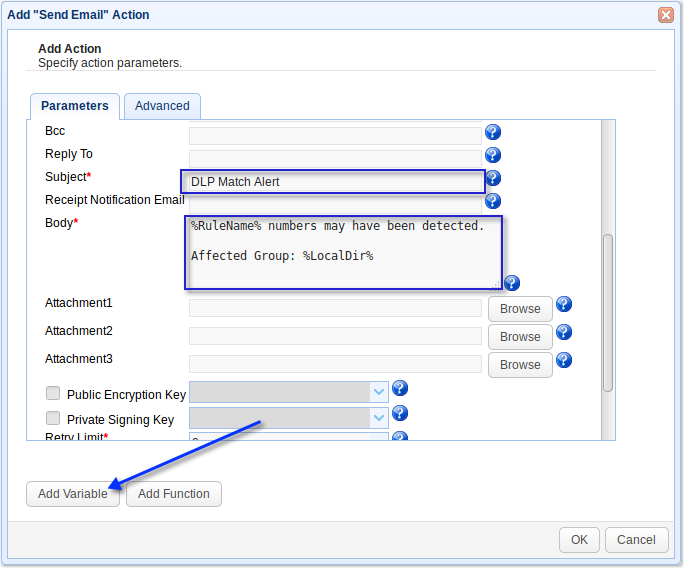
%RuleName% numbers may have been detected.
Affected Group: %LocalDir%
Affected Filename: %LocalPath%
Detection occurred at %Hour%:%Minute% on %DayOfMonth%-%Month%-%Year%
Notice how we've employed a couple of variables (those enclosed in %) to give more factual information regarding the incident. You can access a wide range of variables relevant to the particular trigger being used by clicking the Add Variable button.
Click OK when done.
Your newly created Trigger Action should now be added to the list of Trigger Actions. Click OK.
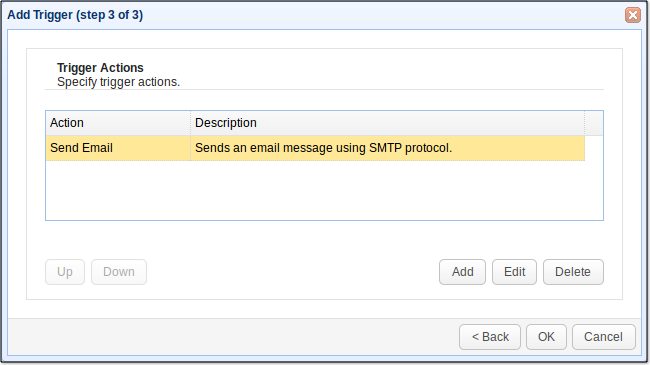
Once you get back to your domain's main screen, make sure you click the Apply button! Otherwise, those changes won't take effect.
That's it. If a user tries to download a file containing credit card numbers from this group folder, an email notification should be sent to the designated recipient. Here's a sample email notification sent by this particular trigger to a Yahoo! Mail account.
Now that you know how to send an email notification to whoever should be notified regarding the DLP match, the next step would be to ensure that the file containing those MasterCard numbers is given a higher level of protection.
Next week in Part 3, I'll show you how to configure JSCAPE MFT Server to automatically encrypt the file using PGP.
Get Started Now
Would you like to try an FTP server that allows you to add DLP rules? Try the free, fully-functional evaluation edition of JSCAPE MFT Server. It supports FTP, FTPS, SFTP, WebDAV, OFTP, AS2, HTTP, HTTPS, and other file transfer protocols.
Download JSCAPE MFT Server Trial