How To Send Big Files For eDiscovery

Overview
Ever since amendments were made to the Federal Rules of Civil Procedure to introduce eDiscovery, litigants and litigators have been struggling to find better ways of handling the large volumes of electronically stored information (ESI) now frequently involved in lawsuits. For instance, many of our clients in the legal profession want to know how to reduce risk exposure when sending big files of ESI.

During an e-discovery process, voluminous ESI files are often shared among clients, attorneys, opposing counsel, and litigation support professionals. This is for the purpose of sharing evidence relevant to the case.
After listening to our clients' specific needs, we've learned that in these sensitive file transfer activities, knowing how to transfer really large files efficiently isn't the only thing parties involved in a lawsuit are concerned with. There are other issues that need to be considered as well.
So we've decided to put together this article in order to help address the seemingly simple issue of sending large files in an e-discovery process.
Why email and cloud file sharing won't do
As mentioned earlier, e-discovery involves lots of files. That's why email would be an impractical solution.
Well, you can actually email big files. However, it's going to take you quite a while to complete a transfer. That's because most email services limit attachments up to only 25 MB. If you have a 1 GB zip file, you'll have to split it up into 25 MB-sized parts first. In fact, typical e-discovery processes can involve tens or even hundreds of Gigabytes.
It's going to be very difficult to manage a large number of attachments. How large can it be, you wonder? If you use an email service with a 25-MB limit on attachments and your total file transfer size is 10 GB, that would translate to a whopping 400 attachments!
Now, some people might point you to the direction of cloud-based file sharing solutions as an alternative to email. These solutions are great for sharing personal files. But if you start sharing ESI, you're bound to encounter data privacy issues.
While the "cloud" sounds like some ethereal place, it's not. It's just another data center (or several data centers) with servers managed by people.
It's hard to tell how secure the data centres holding those files are going to be. Besides, if you use a service like DropBox, copies of those files can be inadvertently shared across multiple devices synced to a single DropBox account. Note that a typical e-discovery process can involve many individuals, so the risk of exposure will only get higher.
Worse, some cloud providers transfer data to offshore locations (to save on operational costs) where legislations for protecting data can be non-existent.
Big file transfers get bigger threat exposure
Another major issue with these tools is that most of them do not provide sufficient data-in-motion protection. Since big file transfers can take hours to complete, there's going to be a considerable time over which sensitive data can be exposed. Chances are, you'll be transmitting your files over the Internet, where serious threats abound.
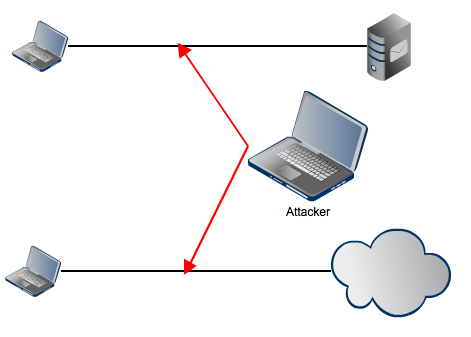
Man-in-the-middle attacks can be launched to view sensitive information or damage its integrity and only can be countered by employing cryptographic network protocols.
Importance of a Data Loss Prevention mechanism
A single Gigabyte can already consist of thousands of files. Some of which may contain privileged or regulation-protected information. Unless the court really orders you to disclose that information, it is your duty to make sure none of it gets to the opposing counsel.
If the opposing party is your client's competitor, your client wouldn't want any trade secret, privileged information or business-critical data to leak unnecessarily to the other side.
Another reason for protecting these file transfers is that some of your clients may be covered by laws like HIPAA, PCI-DSS, GLBA, and state data breach notification laws, which have stringent requirements for protecting certain types of information. If any of that information leaks out, you or you client could face serious penalties.
But because you'll likely be transferring tens of thousands of files, it will be humanly impossible to totally prevent leakage if you rely on manual monitoring alone; moreso if you have to do it under time constraints.
It's therefore important for your file transfer tool to be equipped with DLP (Data Loss Prevention) features, which can automatically detect sensitive information and immediately notify you about it.
The need for high availability
Lengthy file transfers are more likely to suffer from disruptions than short ones. Too many of these disruptions can lead to delays, prevent parties from meeting court deadlines, and force the court to impose sanctions. Hence, preventive as well as contingency measures should be in place.
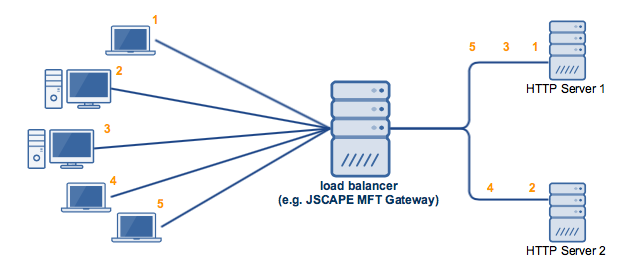
One way to reduce the likelihood of a file transfer service interruption due to an overloaded server is to apply load balancing. Load balancing will allow you to distribute workload across a cluster of servers and consequently minimize the risk of a single server failing due to overload.
Example of two servers whose workloads are distributed via load balancing:
Despite the presence of certain preventive measures, some servers can still fail due to unforeseen circumstances. In these situations, it would be best to have a way to quickly resume data transmission. One way would be to have a failover server that could readily take over if the primary server goes down.
Example of a failover server:
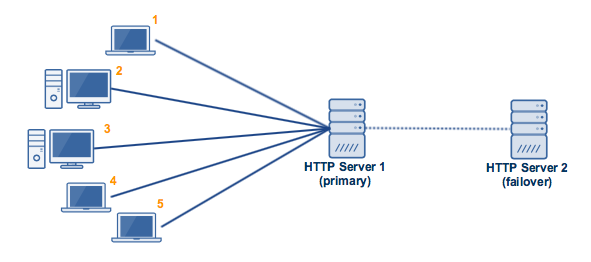
The two high availability configurations shown above were compared in the article Active-Active vs Active-Passive High Availability Cluster. Click that link to learn more about them.
Scheduled, automated uploads and downloads
If you've ever tried uploading or downloading a boatload of files, then I'm sure you know how it can clog your network and disrupt other business operations. That's why the best time to carry out large file transfers is after office hours or during weekends. Unfortunately, that would entail having someone do overtime and administer the file transfers.
That doesn't have to happen if your file transfer server's capable of automated file transfers. That way, you can simply schedule the transfers and go home. If your server allows it, you can configure it to send you email notifications regarding the transfer so you can stay on top of the situation.
Recommended read: How To Get Your MFT Server To Email You About Last Night’s Download
A better way to send big files for e-Discovery
If you're in the legal profession and looking for a better way to send files during e-Discovery, we invite you to try JSCAPE MFT Server.
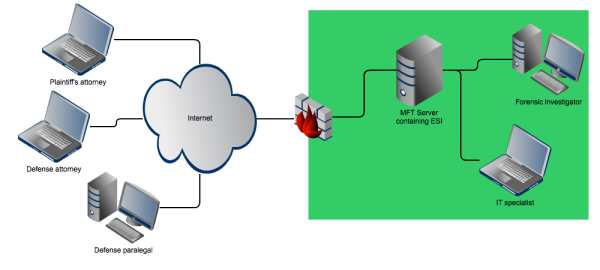
First of all, JSCAPE MFT Server readily supports big file transfers. Once you've connected to it using a file transfer client, you can easily make large multiple-file uploads and share ESI to everyone involved in the eDiscovery process (assuming they've also been granted access to the server) with just a few clicks.
To make sure the transmitted ESI stays secure throughout the entire duration of the transfer, you can employ any of the supported secure file transfer protocols like FTPS, SFTP, SCP, and HTTPS.
JSCAPE MFT Server also comes with a built-in DLP mechanism that will automatically detect sensitive information, strings of text, or patterns of characters deep inside your files by taking advantage of the power of regular expressions.
As soon as sensitive data is detected, the server can automatically prevent unauthorized users from gaining access to the file in question and even notify you through an email or Twitter tweet so you can quickly take appropriate action.
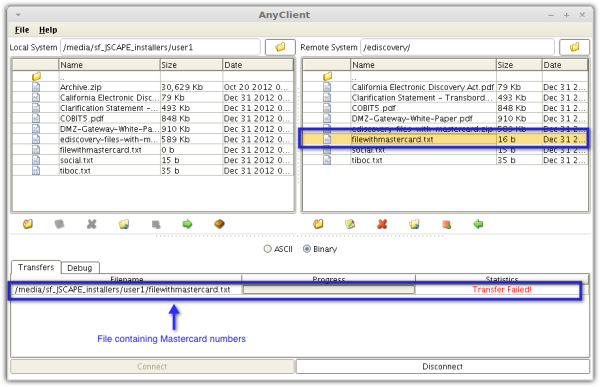
The screenshot below shows a user's attempt at downloading a file containing credit card information. Since JSCAPE MFT Server's DLP mechanism has been activated on the folder holding the said file, the download attempt fails.
JSCAPE has some excellent solutions for high availability. These solutions provide both preventive and contingency measures for network, server or application failure.
Last but not the least, JSCAPE MFT Server comes with a powerful automation-enabling feature called Triggers (click this link for tutorials, examples, and use cases) that supports an extensive array of file transfer tasks. With triggers, you can schedule file transfers, set up email notifications, set up server to server file transfers, automatically secure sensitive uploads, and build a wide variety of automated tasks.
Get Started
JSCAPE MFT Server comes with a FREE, fully-functional evaluation edition that you can try today.
Download JSCAPE MFT Server Trial