Groups and their role in regulatory compliance - Part 1

Overview
Here's something that's particularly useful if you want to provide access control to JSCAPE MFT Server directories based on need to know and according to job responsibilities. It's called Groups. JSCAPE managed file transfer server Groups are named sets of virtual directories and file system permissions that may be assigned to multiple user accounts. You can use them to comply with certain laws and regulations like PCI-DSS, HIPAA, and SOX.
Role in regulatory compliance
The ability to restrict access to certain types of data on a need-to-know basis is often a recommended - and sometimes even required - security measure in data protection laws and regulations.
In PCI-DSS (Payment Card Industry Data Security Standard)
Requirement 7.1 of PCI-DSS v 3.2, for instance, states the need to "Limit access to system components and cardholder data to only those individuals whose job requires such access."
In HIPAA (Health Insurance Portability and Accountability Act)
A similar form of control can be found as a standard in HIPAA's final Security Rule (the part of HIPAA that impacts file transfer systems). The importance of controlling access to ePHI is stipulated in the fourth paper of the Security Rule Educational Series, entitled "Security Standards: Technical Safeguards".
In discussing HIPAA's Access Control standard (§ 164.312(a)(1)), the paper calls for the implementation of "technical policies and procedures for electronic information systems that maintain electronic protected health information to allow access only to those persons or software programs that have been granted access rights..."
In SOX (Sarbanes-Oxley Act)
One of the main reasons why legislators came up with SOX was to bring down incidents of fraud. Therefore, granting employees the least amount of privileges needed to perform a job is an important ingredient when complying with this law.
Assigning access privileges to each individual in your organization might seem pretty simple. But then when you have a large organization, it would be extremely difficult to keep up with promotions, reshufflings, reassignments, resignations, and new hirings, and still make sure people have just the right privileges. Here's an easy way to do it on your managed file transfer system.
A simple example featuring Groups
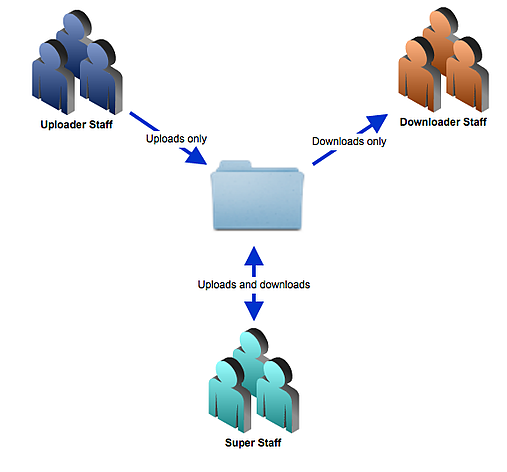
Let me now show you how you would use groups to limit the access permissions of users based on those users' specific functions in your file transfer environment. I'm going to do it using a simplified sample scenario.
In our example, one group of employees is going to be tasked to upload files to our file transfer server. We will call this group the Uploader Staff. In addition to performing uploads, these employees will also be allowed to create directories, delete directories, view files and subdirectories, delete files, rename files and so on. Basically, they will be allowed to do practically everything that can be done on the server except download files.
The only people in our organization who will be allowed to download files will belong to a separate group. This group will be known as the Downloader Staff. Aside from downloading files, members of the Downloader Staff will only be able to view files and subdirectories; nothing more. For instance, they will not be able to upload files, delete files, or even rename files.
Finally, we will have a select group of employees who are going to be allowed to do all the functions of both groups. They shall be called the Super Staff. In a real-world scenario, it's not good for such a group to exist. Employees with super user privileges will naturally pose a very high risk to your organization. Still, we include them here just so we can demonstrate the power of groups.
In our imaginary organization, The Uploader Staff group will consist of Joey and Maria. The Downloader Staff group, on the other hand, will be made up of Steven and Doug. Only one member will belong to the Super Staff: Danika.
Uploader Staff: Joey, Maria
Downloader Staff: Steven, Doug
Super Staff: Danika
Let's now go to Part 2 of this post and watch these groups in action.