Redefining the FTP Server
Overview
Your perception of an FTP server may be in need of an overhaul and you probably need to know why.
Typical FTP server functionality
To transfer files via FTP, a user connects to an FTP server and then logs in using his designated username and password. Sometimes, the server is configured to allow anonymous logins and the user only has to enter “anonymous” for the username and an email address (or no entry at all) for the password.
Once the server has verified the user’s identity through a username-password match in its database, it will then allow the user to:
- ✔ Browse the contents of a directory on the server
- ✔ Transfer to another directory on the server
- ✔ Delete files or directories on the server
- ✔ Create a new directory on the server
- ✔ Copy a file from the user’s client machine to the server (uploading)
- ✔ Copy a file from the server to the client machine (downloading)
Indeed, if we only consider its most common functions, an FTP server can provide almost the same functionality as a local filesystem. The navigational familiarity it allows (especially through GUI FTP clients), in addition to its highly versatile file transfer capabilities (i.e., enabling transfers of extremely large files, multiple files, or entire directories), are the main reasons why the FTP server is very popular in data exchange-intensive industries like Finance, Manufacturing, Transportation, Healthcare, Insurance, and Communications.
To learn How to FTP a File , click that link.
But despite having these attributes, the FTP server most of us are familiar with is actually poorly equipped to meet today’s file transfer requirements. Here's why.
What a traditional FTP server lacks
It all has to do with security, specifically the lack of it.
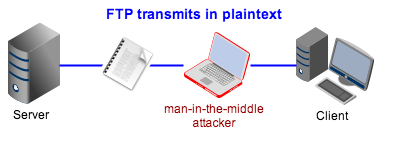
If you examine a traditional FTP server, you'll notice that the only security it really has is the login feature (i.e., username and password), which provides some degree of authentication and thus a way of keeping out unauthorized users.
Well, that might be enough to keep out the average user alright. But not hackers. Not even script kiddies (amateur hackers). Because FTP usernames and passwords are transmitted in plaintext, these crooks only need some basic Man-in-the-Middle Attack skills and a sniffer to eavesdrop on FTP connections for usernames and passwords.
Hacking tool revealing FTP username (user1) and password (demo)
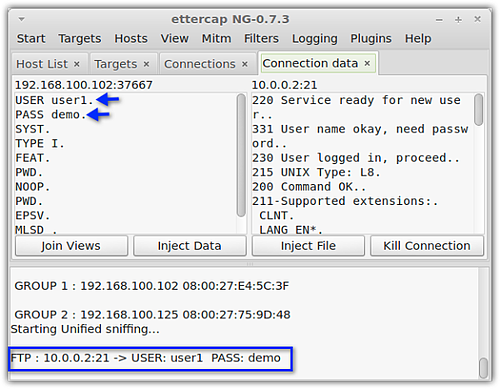
And that's not the only vulnerability. Since FTP allows an unlimited number of logins, hackers are able to exploit this by launching brute force attacks on the server in order to "guess" passwords.
Another inherent FTP vulnerability can be found in Active mode, one of two modes (the other being Passive) that an FTP connection can operate on. To facilitate Active mode, the client-side firewall must be configured to allow inbound connections to internal ports. This could potentially expose machines behind the firewall to incoming attacks. If you want to learn more about Active and Passive FTP modes in relation to firewall security issues, click that link.
There are several other weaknesses. The Anonymous User feature itself is a clear vulnerability since it allows unauthorized users access to the server. We can actually go on but I'm sure you get the point. Simply put, a traditional FTP server is a highly vulnerable machine.
It would've been perfectly fine if all FTP servers were only deployed on LANs that were devoid of threats. Well, first of all, most FTP servers are out there on the Internet where threats abound. Secondly, even LANs are subjected to internal threats these days.
But come to think of it, why are FTP servers so weak? Well, if you really think about it, the first version of the FTP protocol was mainly designed only for the few researchers and military staff who had access to ARPANET. Because this was such a small community, the original developers of the protocol didn't bother to integrate strong security features into it.
Secure FTP and the modern day FTP server
Of course, as soon as FTP was released to the public through the Internet and the vulnerabilities discovered, efforts were made to plug them. This paved the way for what are now known as Secure FTP protocols. There are two main implementations of secure FTP: FTPS and SFTP.
These two secure file transfer protocols were designed to address the main weaknesses of FTP.
For instance, both FTPS and SFTP support encryption, which can prevent hackers from eavesdropping on a file transfer session.
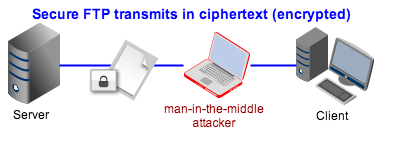
Both protocols also augment the usual username/password method with other methods of authentication. FTPS uses SSL certificates, while SFTP uses SSH keys. Both are based on the same principle, i.e., public key authentication. An additional method of authentication can make it substantially more difficult for hackers to break passwords.
Still, in a world teeming with network-based threats and onerous IT-impacting regulations, these countermeasures are not enough. That's why several security-conscious companies have started hardening their file transfer servers even more. In addition to employing secure FTP protocols, these companies have started implementing machine-enforced password policies, enabling Passive mode FTP, automating virus scans, using data loss prevention mechanisms, and a host of other security countermeasures.
Today, when you go to one of these companies and ask a non-technical user how they do bulk file transfers, chances are they'll tell you they use FTP. That's because, even with all those security measures, the basic functionality hasn't really changed. But if you ask network admins about their file transfer server, you'll discover it's no longer plain FTP internally. In fact, they're probably not using the regular FTP protocol anymore.
These modern day FTP servers can put you in a better position in meeting stringent privacy and security requirements. If your file transfer server does not yet meet the description of a modern day FTP server, it's time it did.
Recommended Downloads
JSCAPE MFT Server is a powerful platform-independent managed file transfer server that supports FTP and secure FTP (FTPS and SFTP). It comes with a wide range of security features, including those mentioned above. It also has a free fully-functional evaluation edition, which you can download today.